The rise of quantum computing poses a significant, though not immediate, threat to many of the cryptographic systems that underpin modern digital security. Among the most vulnerable are those relying on elliptic curve cryptography (ECC), a widely used method for securing communications and transactions, including many cryptocurrencies. The core challenge lies in the potential for quantum computers to efficiently solve the mathematical problems that currently protect ECC, potentially exposing sensitive data and funds. Addressing this requires proactive measures to transition to quantum-resistant algorithms, a complex undertaking that is now gaining momentum. Securing elliptic curve cryptocurrencies against quantum vulnerabilities is a critical step in ensuring the long-term viability of these systems.
ECC’s popularity stems from its ability to provide strong security with relatively modest key sizes, making it ideal for resource-constrained environments like mobile devices and embedded systems. Though, this efficiency comes at a cost. Peter Shor’s algorithm, developed in 1994, demonstrates that a sufficiently powerful quantum computer could break many of the public-key cryptosystems currently in use, including those based on ECC and RSA. While building such a computer remains a substantial technological hurdle, the potential impact is so severe that researchers and developers are already working on mitigation strategies. The National Institute of Standards and Technology (NIST) has been leading a multi-year effort to standardize new, quantum-resistant cryptographic algorithms.
The Quantum Threat to Elliptic Curve Cryptography
Traditional cryptography relies on the computational difficulty of certain mathematical problems. For ECC, the security rests on the difficulty of the elliptic curve discrete logarithm problem. Essentially, given a point on an elliptic curve and a base point, it’s computationally hard to discover the scalar that, when multiplied by the base point, results in the given point. Classical computers struggle with this problem as the key size increases. However, Shor’s algorithm provides a quantum solution that dramatically reduces the computational complexity, rendering ECC vulnerable.
The implications for cryptocurrencies are substantial. Many cryptocurrencies, including Bitcoin and Ethereum, utilize ECC to secure transactions and control the creation of new units. If a quantum computer were able to break the ECC used in these systems, it could potentially forge transactions, steal funds, and disrupt the entire network. While Bitcoin’s reliance on ECC is somewhat mitigated by its use of hash functions (which are considered more resistant to quantum attacks, though not entirely immune), Ethereum’s transition to Proof-of-Stake and the increasing complexity of smart contracts heighten the urgency of addressing quantum vulnerabilities.
NIST’s Post-Quantum Cryptography Standardization
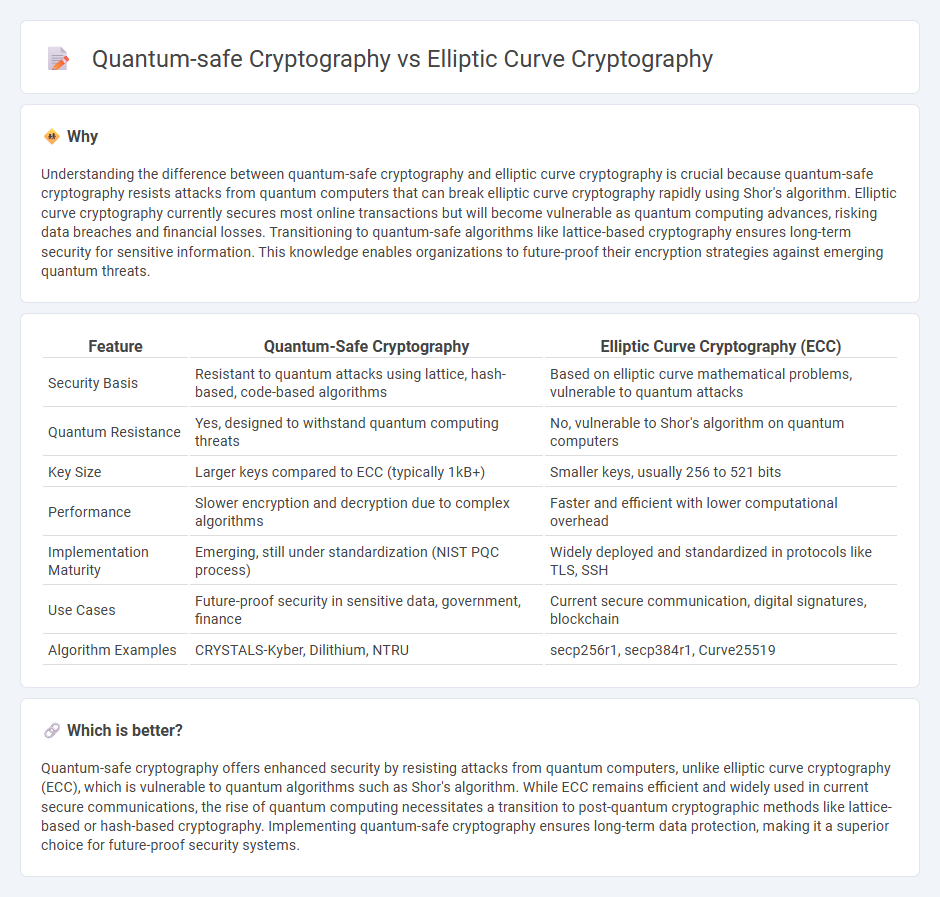
Recognizing the looming threat, NIST launched a post-quantum cryptography (PQC) standardization process in 2016. After multiple rounds of evaluation, NIST announced its initial set of standardized algorithms in 2022, with further selections expected. These algorithms fall into several categories, including lattice-based cryptography, code-based cryptography, multivariate cryptography, and hash-based signatures. The initial selections – CRYSTALS-Kyber (for key encapsulation) and CRYSTALS-Dilithium, FALCON, and SPHINCS+ (for digital signatures) – represent a significant step towards a quantum-resistant future.
The transition to these new algorithms is not without its challenges. The PQC algorithms generally require larger key sizes and computational resources than ECC, which could impact performance and scalability. The algorithms are relatively new, and their long-term security is still being evaluated. Ongoing research and analysis are crucial to identify and address any potential vulnerabilities.
Strategies for Securing Cryptocurrencies
Several strategies are being explored to mitigate the quantum threat to cryptocurrencies. These include:
- Hybrid Approaches: Combining ECC with PQC algorithms to provide an interim layer of security. This allows for a gradual transition while maintaining compatibility with existing infrastructure.
- Key Rotation: Regularly changing cryptographic keys to limit the window of opportunity for an attacker.
- Quantum Key Distribution (QKD): A method of securely distributing cryptographic keys using the principles of quantum mechanics. While promising, QKD is currently limited by distance and cost.
- Algorithm Agility: Designing systems that can easily switch between different cryptographic algorithms as new threats emerge or better algorithms become available.
Ethereum, for example, is actively researching and planning for a transition to quantum-resistant cryptography. Developers are exploring various PQC algorithms and considering how to integrate them into the Ethereum Virtual Machine (EVM). The Ethereum Foundation has been involved in discussions and workshops focused on PQC, and several proposals for quantum-resistant upgrades are under consideration. Ethereum’s research into quantum resistance highlights the complexity of the challenge and the need for a coordinated effort.
The Role of Layer-2 Solutions
Layer-2 scaling solutions, such as rollups, may offer a more flexible environment for implementing quantum-resistant cryptography. These solutions operate on top of the main blockchain and can be updated more easily without requiring a hard fork of the underlying protocol. This agility could be crucial for quickly responding to new quantum threats or adopting improved PQC algorithms.
Looking Ahead
The threat of quantum computers breaking current encryption standards is not a question of *if*, but *when*. While a practical, cryptographically relevant quantum computer is still years away, the time to prepare is now. The ongoing standardization efforts by NIST, coupled with the research and development within the cryptocurrency community, are essential steps towards building a quantum-resistant future. The next key milestone will be the continued implementation and testing of the NIST-selected PQC algorithms in real-world applications, including blockchain technologies.
The transition to post-quantum cryptography will be a complex and ongoing process, requiring collaboration between researchers, developers, and policymakers. Staying informed about the latest developments and actively participating in the discussion are crucial for ensuring the long-term security and resilience of our digital infrastructure.
Do you have thoughts on the future of quantum-resistant cryptography? Share your comments below, and please share this article with your network.