Security researchers have uncovered a sophisticated new Lua-based malware, dubbed LucidRook, currently being deployed in highly targeted spear-phishing campaigns. The attacks are specifically aimed at universities and non-governmental organizations (NGOs) in Taiwan, utilizing a modular design that allows attackers to pivot their tactics in real-time without alerting defenders.
The malware is the operate of a threat actor tracked as UAT-10362. According to researchers at Cisco Talos, this group demonstrates mature operational tradecraft, employing a combination of social engineering and technical obfuscation to bypass traditional security perimeters.
First observed in October 2025, the campaign relies on password-protected archives delivered via phishing emails. By locking the malicious payloads inside encrypted archives, the attackers can often bypass automated email scanners that cannot inspect the contents of the files without the password, which is typically provided in the body of the email to entice the victim.
Dual Infection Vectors and Social Engineering
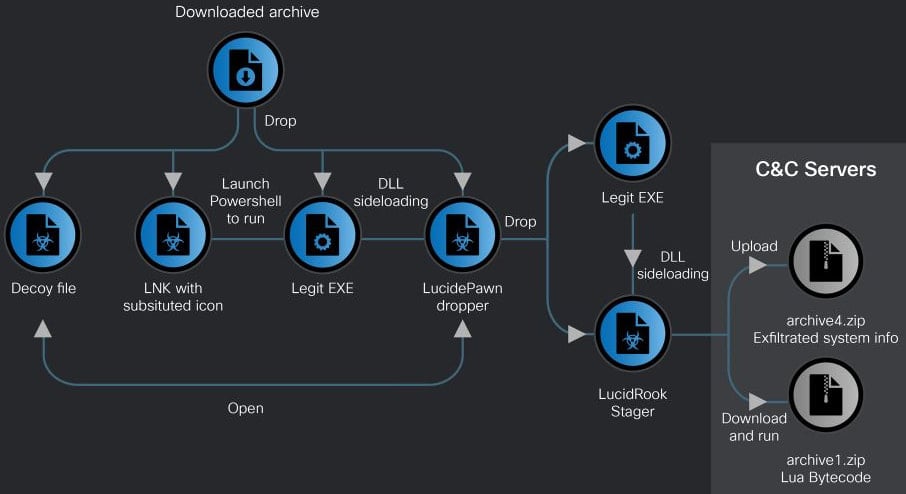
The UAT-10362 group utilizes two distinct infection chains to gain a foothold on target systems. The first relies on LNK shortcut files. In this scenario, the attackers leverage decoy documents—specifically government letters designed to look like official correspondence from the Taiwanese government—to distract the user while the malware executes in the background.
This LNK-based attack eventually delivers a dropper known as LucidPawn. Once active, LucidPawn decrypts and deploys a legitimate executable that has been renamed to mimic Microsoft Edge. To actually launch the primary malware, the dropper uses a malicious DLL (DismCore.dll) for sideloading LucidRook, a technique that allows the malware to run under the guise of a trusted process.
Source: Cisco Talos
The second infection chain is more direct, utilizing an EXE-based approach. In these instances, the attackers leverage a fake antivirus executable that impersonates Trend Micro Worry-Free Business Security Services. By mimicking a trusted security product, the attackers exploit the user’s trust in their own security software to convince them to execute the malicious file.
The Technical Edge: Lua Bytecode and Stealth
From a technical perspective, LucidRook is notable for its use of a built-in Lua execution environment. Rather than delivering a static set of instructions, the malware retrieves and executes second-stage payloads as Lua bytecode. This modularity provides the threat actor with a significant strategic advantage.
By embedding the Lua interpreter, the attackers effectively turn the native DLL into a stable platform. This allows them to update or tailor the behavior of the malware for specific targets or different campaigns by simply updating the Lua bytecode payload, rather than rewriting the core malware code.
“Embedding the Lua interpreter effectively turns the native DLL into a stable execution platform while allowing the threat actor to update or tailor behavior for each target or campaigns by updating the Lua bytecode payload with a lighter and more flexible development process,” Cisco Talos explains.
This architecture also enhances operational security (OPSEC). As the Lua stage can be hosted only briefly and removed from the command-and-control (C2) server immediately after delivery, forensic investigators who recover the loader may locate it impossible to reconstruct the full attack because the externally delivered Lua payload is gone.
To further complicate reverse-engineering, the binary is heavily obfuscated. The group has masked embedded strings, file extensions, internal identifiers, and C2 addresses, making it difficult for security analysts to determine where the data is being sent or how the malware communicates.
Reconnaissance and Data Exfiltration
Once LucidRook has established a presence on a system, it begins a phase of deep system reconnaissance. The malware collects a wide array of sensitive information, including:
- User and computer names.
- A comprehensive list of installed applications.
- A snapshot of all currently running processes.
To ensure the stolen data is not intercepted, the malware encrypts the findings using RSA and stores them in password-protected archives. This data is then exfiltrated to attacker-controlled infrastructure via File Transfer Protocol (FTP).
During their analysis, researchers also identified a companion tool named “LucidKnight.” While LucidRook handles the primary infection and execution, LucidKnight appears to be dedicated to reconnaissance. Interestingly, LucidKnight abuses the Gmail SMTP (GMTP) protocol to exfiltrate data, suggesting that UAT-10362 maintains a flexible toolkit that can switch between FTP and email-based exfiltration depending on the target’s network restrictions.
Campaign Summary: LucidRook Overview
| Component | Function | Key Technique |
|---|---|---|
| LucidPawn | Initial Dropper | DLL Sideloading (DismCore.dll) |
| LucidRook | Primary Malware | Lua Bytecode Execution |
| LucidKnight | Reconnaissance | Gmail SMTP Exfiltration |
| Decoys | Social Engineering | Fake Taiwanese Govt Letters |
What Remains Unknown
Despite the detailed analysis of the delivery and reconnaissance phases, a critical gap remains in the understanding of the attack’s ultimate goal. Cisco Talos stated they have medium confidence that these attacks are part of a targeted intrusion campaign, but they were unable to capture a decryptable Lua bytecode payload fetched by LucidRook.
Because the bytecode is delivered dynamically and then removed, the specific “post-infection” actions—whether the goal was espionage, financial theft, or the deployment of ransomware—remain unknown. This underscores the effectiveness of the group’s stealth-centric approach.
Organizations in Taiwan, particularly those in the academic and NGO sectors, are advised to exercise extreme caution with password-protected archives and to monitor for unusual FTP traffic or unauthorized use of Gmail SMTP services within their networks.
Further updates on this campaign are expected as security researchers continue to monitor C2 infrastructure and attempt to capture live Lua payloads for decryption.
Do you have information about this campaign or similar phishing attempts? Share your insights in the comments below or contact our newsroom.

