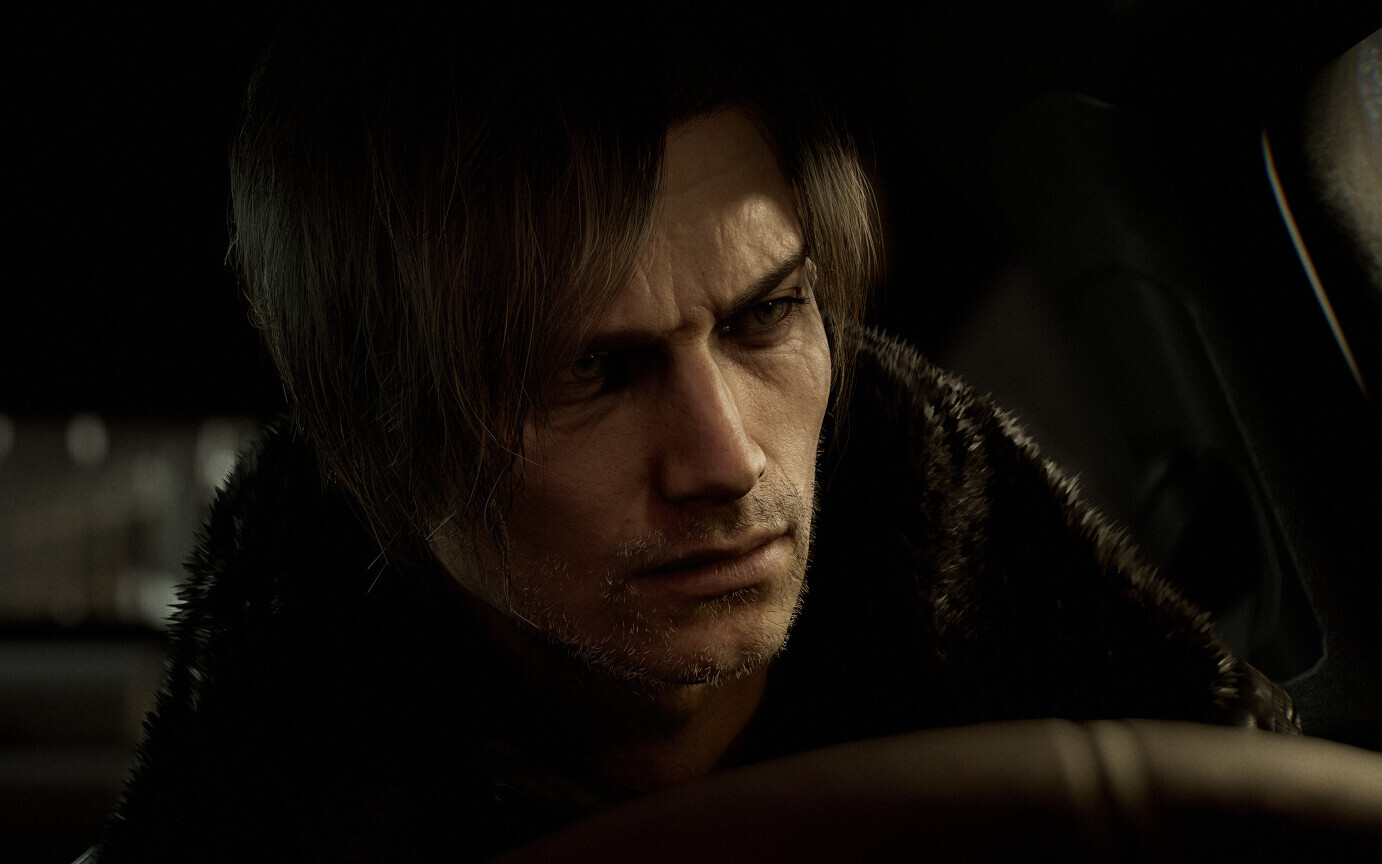
A hacker operating under the pseudonym voices38 has reportedly breached the Denuvo anti-tamper protections on Resident Evil Requiem, making it the first major title of 2026 to be cracked. The announcement, shared via Reddit approximately six weeks after the game’s official launch, has sent ripples through both the gaming community and the software security industry.
The breach is particularly notable not just for the title affected, but for the method employed. While recent bypasses have leaned heavily on hypervisor-based workarounds—which essentially run the game within a virtualized environment to deceive the DRM—voices38 claims to have developed a “clean,” traditional crack. This approach removes the protection layers entirely, allowing the software to run natively without the stability risks or system overhead associated with emulation.
For those of us who spent years in software engineering before moving into reporting, this distinction is critical. Hypervisor bypasses are often seen as a “brute force” logic shift; they don’t so much break the lock as they do trick the door into thinking the key has already been turned. A clean crack, however, requires a deep architectural understanding of the game’s binary and the DRM’s specific triggers. According to the reports, the process took voices38 only two weeks, a timeline that suggests a significant vulnerability in the current iteration of the software.
The Technical Evolution of Denuvo in 2026
The breach provides a rare glimpse into the current state of Digital Rights Management (DRM). In the technical breakdown shared by voices38, the hacker noted that the 2026 version of Denuvo appears to have evolved very little from its 2025 predecessor. The analysis suggests that only two additional protective functions were implemented in the latest update.

This stagnation is a point of contention for many in the PC gaming space. Denuvo, owned by Irdeto, has long been criticized by players for its potential to degrade CPU performance and increase load times. The perception is that the software consumes vital system resources to constantly verify the legitimacy of the license, often at the expense of the user’s frame rate.
Despite these complaints, the industry’s reliance on the technology remains steadfast. Developers for upcoming titles, including Crimson Desert and Pragmata, continue to integrate the system. The primary goal for publishers like Capcom is the protection of the “launch window”—the first few weeks of sales where the vast majority of a game’s revenue is generated. In the case of Resident Evil Requiem, that window remained largely intact for a month and a half, though the eventual crack proves that no digital lock is permanent.
Comparing DRM Breach Trends
The fall of Resident Evil Requiem places it in an exclusive category of recent high-profile breaches. For much of the last year, Denuvo has remained largely impenetrable, with very few titles seeing a successful bypass.
| Game Title | Release Year | Crack Method | Time to Breach |
|---|---|---|---|
| Doom: The Dark Ages | 2025 | Hypervisor/Hybrid | Varies |
| Resident Evil Requiem | 2026 | Clean Crack | 2 Weeks |
Impact on Performance and Consumer Experience
Beyond the ethics of piracy, the removal of DRM often leads to a tangible increase in game performance. When Denuvo is stripped from a build, the CPU no longer has to execute the constant integrity checks that the software requires. For a demanding title like Resident Evil Requiem, this could mean smoother frame pacing and reduced stuttering on mid-range hardware.
This creates a complex situation for Capcom. Now that the protections have been compromised, there is increasing pressure from the community to officially remove the DRM from the PC version. Removing the software in an official patch would not only reward legitimate buyers with a more performant experience but would also signal a shift in how the company views the long-term value of its digital protections versus the immediate needs of its user base.
The Stakeholders in the DRM War
- Publishers: Prioritize the initial sales spike and seek to minimize “Day 1” piracy.
- Security Firms: Aim to create an “unbreakable” shell to maintain their market value and contracts.
- Players: Desire maximum hardware performance and permanent ownership of their software.
- Crackers: Often driven by technical prestige and the desire to “liberate” software from restrictive locks.
The success of voices38 serves as a reminder that the relationship between security software and those who seek to dismantle It’s a perpetual arms race. Every new “feature” added to a DRM system eventually becomes a puzzle for a dedicated engineer to solve. The speed with which this 2026 iteration was dismantled suggests that the “cat-and-mouse” game is currently tilting in favor of the mouse.
Whether Capcom chooses to respond with a new security update or simply removes the DRM to improve the game’s stability remains to be seen. The industry will be watching closely to see if other 2026 releases follow the same path, or if this breach was an isolated incident of exceptional technical skill.
The next major checkpoint for the community will be the upcoming performance benchmarks comparing the original DRM-protected version of the game against the cracked build, which are expected to be released by independent testers in the coming days.
Do you think DRM does more harm than good for PC gaming? Share your thoughts in the comments below.