The very tools developers use to secure their code and connect their applications have develop into the primary vectors for some of the most expansive security breaches of the year. In a series of coordinated open source supply chain attacks throughout March, two distinct threat actors poisoned widely used libraries and scanners, stealing secrets from more than 10,000 organizations.
These incidents represent a shift in adversary strategy, moving away from trying to breach the perimeter of a single corporation and instead targeting the “single points of failure” in the global software ecosystem: the open source maintainers and the security tools embedded in thousands of CI/CD pipelines.
The scale of the exposure is staggering. One target, the JavaScript library Axios, sees roughly 100 million weekly downloads and is integrated into an estimated 80 percent of cloud and code environments. The other, a vulnerability scanner called Trivy, is used by over 100,000 contributors and organizations to find bugs in their own software. When these tools are compromised, the malware is delivered with an implicit seal of trust, bypassing many traditional security checks.
According to Charles Carmakal, CTO of Mandiant Consulting, the full impact of these breaches will not be understood for months. The data exfiltrated during these windows is often stockpiled and leveraged slowly, meaning the blast radius will likely continue to expand as attackers use stolen credentials to move laterally into novel environments.
The ‘Smash-and-Grab’ of TeamPCP
The first wave of attacks was carried out by a group known as TeamPCP, a loosely knit collective of young, English-speaking attackers who mirror the brash, influencer-style communication of groups like Lapsus$. Unlike state-sponsored actors who prefer to remain hidden, TeamPCP often brags about its exploits on Discord and Telegram, even embedding a “Rickroll” video in its malicious domains.
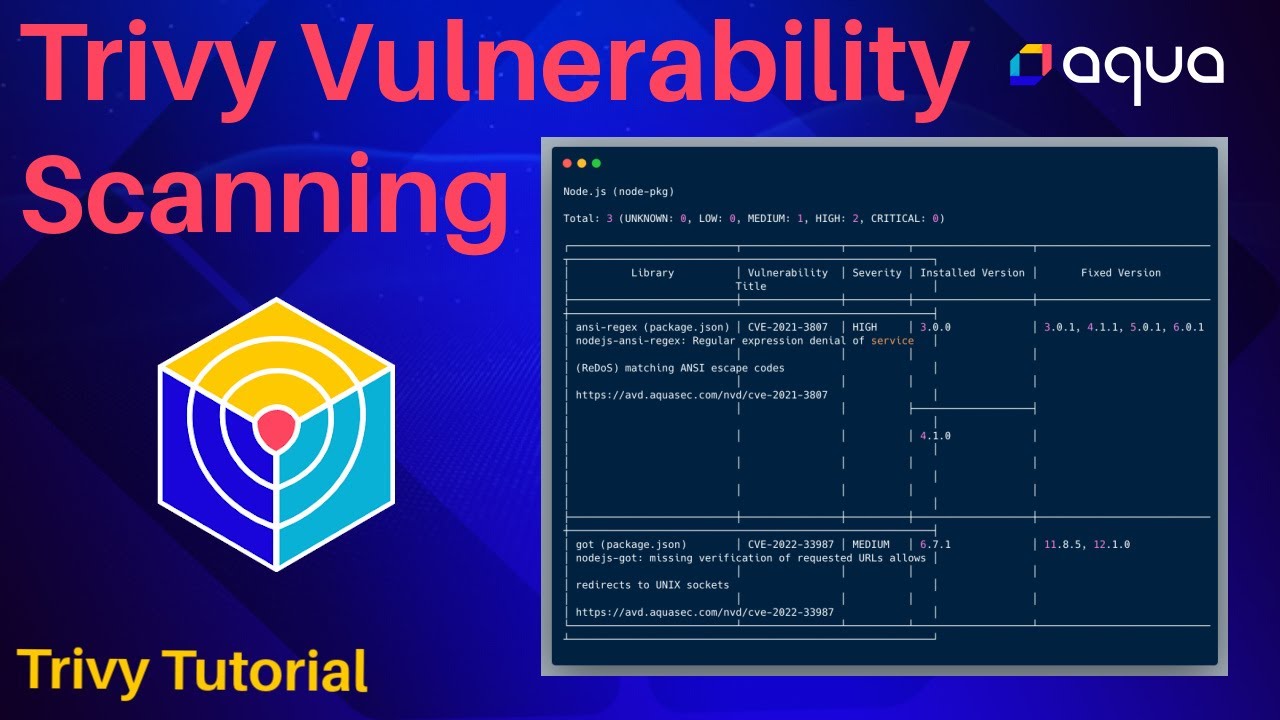
Their campaign began in late February when they compromised Trivy, an open source vulnerability scanner maintained by Aqua Security. On March 16, the group injected credential-stealing malware into the scanner’s binary, container images, and GitHub Actions. This allowed them to “hoover up” SSH keys, Kubernetes configuration files, and cloud credentials directly from the developers’ machines and pipelines.
TeamPCP then used the secrets stolen from Trivy to launch a cascading series of attacks. On March 23, they pivoted to KICS, a static analysis tool maintained by Checkmarx. Shortly after, they published malicious versions of LiteLLM and Telnyx to the Python Package Index (PyPI). Both of these projects utilized Trivy in their own CI/CD pipelines, creating a domino effect of compromise.
Ben Read, who leads the cyber threat intel team at Wiz, suggests that targeting security tools may have been a deliberate choice. Read noted that security environments are often where “odd things happen,” and because they are designed to handle anomalies, malicious activity might be overlooked by administrators.
While the group’s methods were described as “smash-and-grab” due to their speed and lack of stealth, the volume of data was immense. Carmakal estimates that credentials for more than 10,000 organizations were stolen, a haul so large that TeamPCP reportedly began soliciting other threat actors to help monetize the stolen access.
AI-Driven Deception and the Axios Breach
While TeamPCP focused on volume and speed, a second attack on March 31 demonstrated a high level of psychological sophistication. Attackers hijacked the account of a maintainer for Axios, one of the most popular HTTP client libraries on npm, and slipped a remote-access trojan (RAT) into two legitimate releases.
Google’s Threat Intelligence Group attributed this operation to UNC1069, a suspected North Korean threat actor. The attack did not start with a technical exploit, but with a meticulously crafted social engineering campaign targeting the project’s primary maintainer, Jason Saayman.
The attackers created a digital clone of a real company and its founders, including a realistic Slack workspace complete with employee profiles. After gaining Saayman’s trust through an invitation to collaborate, they lured him into a Microsoft Teams meeting. Upon joining, a fake notification informed Saayman that his software was out of date; the “update” he installed was, in fact, the RAT.
Once the attackers had access to Saayman’s machine, they pushed malicious updates to the Axios project. For a three-hour window, any system that installed the compromised packages downloaded a stealer designed to exfiltrate private keys and credentials to an attacker-controlled server.
| Feature | TeamPCP Campaign | UNC1069 Campaign |
|---|---|---|
| Primary Target | Trivy (Security Scanner) | Axios (JS Library) |
| Attacker Profile | Financially motivated collective | North Korean-linked (State) |
| Primary Method | CI/CD secret theft & pivoting | AI-enabled social engineering |
| Key Goal | Credential theft & extortion | Private key & crypto theft |
| Detection Time | Under 12 hours | Approx. 3 hours |
The Developer as the New Perimeter
These attacks underscore a growing trend: the developer is now the primary target. Nick Biasini, outreach lead at Cisco Talos, notes that attackers are increasingly focusing on the supply chain because it provides a force-multiplier effect. Compromising one maintainer can grant access to thousands of downstream organizations.
This is particularly evident in the “flywheel” of North Korean operations. These actors have spent years infiltrating companies as fake IT workers to learn the inner workings of developer environments. By combining this technical knowledge with AI—which allows them to create hyper-personalized lures and deepfake personas—they can bypass the skepticism of even experienced engineers.
The risk is compounded by the democratization of development. As non-technical employees use LLMs to write code and spin up cloud environments, the number of potential entry points for attackers increases, often without a corresponding increase in security oversight.
Defending the Poisoned Well
Security experts argue that the only way to mitigate these risks is to move toward a “zero trust” approach for third-party code. One primary recommendation is the adoption of a Software Bill of Materials (SBOM), which acts as an ingredients list for all components within a piece of software. An SBOM allows a company to instantly identify if a compromised package like Axios or Trivy is running anywhere in their environment during a crisis.
Beyond SBOMs, some experts suggest a “delay rule” for updates. Ben Read suggests that if organizations implemented a policy of not downloading any package versions newer than 24 hours, they would have avoided both the Axios and Trivy infections, as both were detected and neutralized within 12 hours.
However, the human element remains the hardest to secure. Biasini warns that social engineering will only worsen as voice and video cloning become more accessible. He suggests that organizations implement “secure objects”—physical items known only to the parties on a call—to verify identity in an era where a CEO’s face and voice can be perfectly synthesized by AI.
The industry is now awaiting further analysis from Google’s Threat Intelligence Group and Mandiant to determine the full list of downstream victims from the Axios breach. As these findings emerge, the focus will likely shift toward creating more robust, multi-signature requirements for updates to critical open source infrastructure.
Do you use a 24-hour delay for your dependency updates, or do you rely on automated patching? Share your thoughts in the comments.

