Hardware enthusiasts and system builders frequently rely on CPUID’s suite of tools to verify processor specs and monitor thermal performance. However, a recent security breach turned these trusted utilities into delivery vehicles for a sophisticated remote access trojan (RAT), as the CPUID website hacked to serve malware through compromised download links.
The incident occurred between April 9 at 15:00 UTC and April 10 at approximately 10:00 UTC. During this window, attackers gained access to a secondary API on the CPUID website, allowing them to swap legitimate installer links for malicious ones. While the company’s original signed binaries remained untouched, users who clicked the download buttons during this period were redirected to a malicious infrastructure designed to bypass traditional security hurdles.
For those of us who have spent years in software engineering, this specific attack vector is particularly insidious. The hackers didn’t need to crack the encryption of the software itself; they simply hijacked the “handshake” between the user and the server. By the time a user realized they weren’t installing the expected utility, the malware had already established a foothold in their system.
The Anatomy of the Attack: DLL Sideloading and STX RAT
The delivery mechanism was a multi-stage operation designed to evade endpoint detection and antivirus software. According to analysis by Kaspersky, the malicious links funneled users through Cloudflare R2 storage, where they downloaded a fake HWiNFO installer named “HWiNFO_Monitor_Setup.” This file was wrapped in a Russian Inno Setup installer to appear legitimate.

Once executed, the package employed a technique known as DLL sideloading. The installer contained a legitimately signed executable, which served as a “trojan horse” to load a malicious library called CRYPTBASE.dll. Because the primary executable was signed and trusted, many security programs ignored the action of it loading the accompanying malicious DLL.
The CRYPTBASE.dll file performed anti-sandbox checks to ensure it wasn’t being analyzed by security researchers before connecting to a command-and-control (C2) server. The final payload delivered was the STX RAT, a remote access trojan with infostealer capabilities. This malware operates primarily in memory, leaving a minimal footprint on the physical hard drive, which makes it significantly harder for standard antivirus scans to detect after the initial infection.
Affected Software Versions
The breach specifically targeted the download paths for four of CPUID’s most popular tools. Users should check their installation dates and version numbers against the following list:
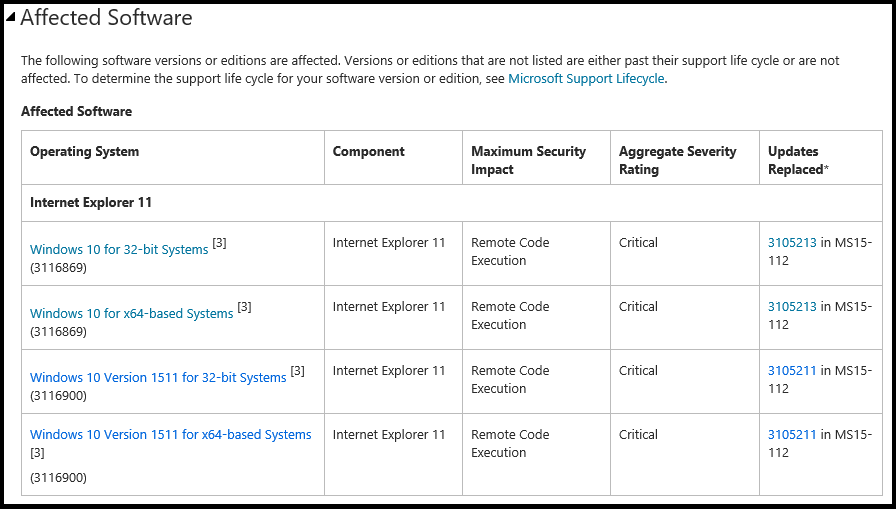
| Software Utility | Compromised Version |
|---|---|
| CPU-Z | Version 2.19 |
| HWMonitor Pro | Version 1.57 |
| HWMonitor | Version 1.63 |
| PerfMonitor | Version 2.04 |
Scope of Impact and Threat Actor Attribution
The scale of the attack appears limited but targeted. Kaspersky estimates that over 150 users downloaded the malicious variants. The victims were not concentrated in one sector; they included individuals and organizations across retail, manufacturing, consulting, telecommunications, and agriculture. Geographically, the majority of the impact was felt in Brazil, Russia, and China.
The sophistication of the campaign suggests a recurring threat actor. Researchers at vxunderground and Igor’s Labs independently verified the download chain and noted a critical piece of evidence: the command-and-control address used in the CPUID attack matches one observed in a March campaign. That previous attack involved a fake FileZilla website used to distribute malware, suggesting the same group is targeting widely used open-source and utility software to cast a wide net.
On VirusTotal, the malicious ZIP file was flagged by 20 different antivirus engines, with some identifying it as the Tedy Trojan and others as the Artemis Trojan, highlighting the evolving nature of the STX RAT’s signature.
Recovery and Next Steps for Users
CPUID has since confirmed that the compromised API has been fixed and the website is now serving clean, legitimate versions of all its tools. Because the original signed binaries were never altered, users who downloaded the software outside of the April 9–10 window are not at risk.
However, if you downloaded any of the affected tools during that timeframe, your system should be considered potentially compromised. The STX RAT’s ability to steal sensitive information and operate in memory means that a simple reboot may not be sufficient to clear the threat.
Affected users are encouraged to take the following steps:
- Perform a Deep Scan: Employ a reputable EDR (Endpoint Detection and Response) tool or a comprehensive antivirus scanner to look for indicators of compromise (IoCs).
- Check for Unfamiliar DLLs: Look for
CRYPTBASE.dllin directories where it does not belong. - Update Credentials: Since STX RAT has infostealer capabilities, changing passwords for sensitive accounts (email, banking, corporate logins) is a prudent precaution.
- Review Network Logs: For corporate users, check for unauthorized connections to unknown external IP addresses that may indicate C2 communication.
As the cybersecurity landscape shifts toward targeting the supply chain and the “delivery” phase of software acquisition, this incident serves as a reminder that even a trusted download button can be a vulnerability. The next confirmed checkpoint for the community will be the release of more detailed indicators of compromise from security firms to help users fully purge the STX RAT from affected systems.
Have you encountered similar issues with hardware utilities recently? Share your experience in the comments or reach out to our tech desk.