The window between the public disclosure of a security vulnerability and its active exploitation is shrinking to a matter of hours. In the case of Marimo, an open-source reactive Python notebook platform, that window was less than 10 hours.
Security researchers have identified a critical Marimo pre-auth RCE flaw that allows unauthenticated attackers to execute arbitrary code on a target system. The vulnerability, tracked as CVE-2026-39987, carries a critical severity score of 9.3 out of 10, reflecting the ease of exploitation and the potential for total system compromise.
As a former software engineer, I’ve seen how “convenience features” in developer tools can accidentally become open doors for attackers. In this instance, a feature intended to provide interactive terminal access became a direct highway for hackers to exfiltrate sensitive cloud credentials and SSH keys from the machines of data scientists and AI researchers.
The flaw affects Marimo versions 0.20.4 and earlier. While the developers released a fix in version 0.23.0 shortly after the April 8 disclosure, the speed with which attackers weaponized the developer’s own advisory serves as a stark reminder of the risks inherent in exposing development environments to the open web.
The mechanics of the breach: An open terminal
The root of the problem lies in a specific WebSocket endpoint: /terminal/ws. In affected versions of Marimo, this endpoint exposes an interactive terminal without requiring any authentication. For an attacker, This represents the ideal scenario; they do not need a password, a token, or a stolen session cookie to gain inside.
Once a connection is established via this endpoint, the attacker gains direct access to a full interactive shell. Crucially, this shell runs with the same privileges as the Marimo process itself. If Marimo is running as a user with administrative or broad system access, the attacker effectively inherits those permissions.
The risk is particularly acute for users who deploy Marimo as an editable notebook or those who expose the platform to a shared network using the --host 0.0.0.0 flag while in edit mode. In these configurations, the /terminal/ws endpoint is visible to anyone who can reach the server’s IP address.
Anatomy of a ‘methodical’ attack
Data from cloud-security firm Sysdig reveals a chillingly efficient exploitation timeline. Within just 12 hours of the vulnerability being made public, 125 different IP addresses were observed conducting reconnaissance, scanning for vulnerable Marimo instances.
The actual exploitation happened even faster. Less than 10 hours after disclosure, researchers spotted the first attempt to steal credentials. The attack followed a precise, manual sequence rather than the clumsy patterns typical of automated botnets.
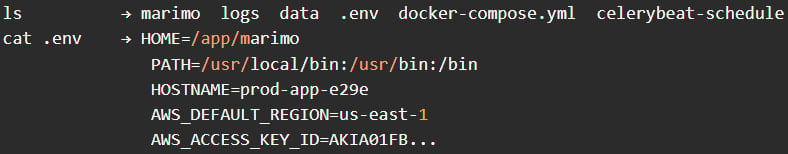
The operator first used a short scripted sequence to validate that the /terminal/ws endpoint was open and that remote command execution was possible. Once confirmed, the attacker disconnected and returned shortly after for a manual deep dive. They began with basic environmental reconnaissance—using commands like pwd, whoami, and ls—to map the directory structure and identify the user’s identity.
The primary objective was clearly high-value data. The attacker immediately targeted .env files, which developers frequently employ to store environment variables, API keys, and cloud provider secrets. By extracting these variables, the attacker could potentially pivot from a single notebook instance to an entire cloud infrastructure.
Sysdig notes that the entire credential access phase was completed in under three minutes. Interestingly, the attacker did not attempt to install a backdoor or deploy cryptominers, suggesting a stealthy operation designed for data theft rather than system disruption.
Who is at risk and how to respond
Marimo has grown in popularity among ML/AI practitioners and researchers, boasting 20,000 GitHub stars. Because these users often handle massive datasets and sensitive API keys for LLMs or cloud compute, the impact of a credential leak can be catastrophic.

If you are using Marimo, the priority is immediate remediation. The following steps are recommended to secure your environment:
- Update Immediately: Upgrade to version 0.23.0 or later. This version closes the unauthenticated access to the terminal endpoint.
- Rotate All Secrets: If you were running a vulnerable version on a network-exposed host, assume your
.envfiles and SSH keys have been compromised. Rotate every API key, password, and token associated with that environment. - Restrict Network Access: Avoid using
--host 0.0.0.0unless absolutely necessary. Use a firewall to restrict access to the Marimo port to trusted IP addresses only. - Emergency Mitigation: If an immediate update is not possible, use a web application firewall (WAF) or network rule to block all traffic to the
/terminal/wsendpoint.
Summary of CVE-2026-39987
| Detail | Information |
|---|---|
| CVE ID | CVE-2026-39987 |
| Severity Score | 9.3 (Critical) |
| Affected Versions | 0.20.4 and earlier |
| Fixed Version | 0.23.0 |
| Primary Risk | Unauthenticated Remote Code Execution (RCE) |
The broader lesson for the AI community
This incident highlights a recurring tension in the modern AI stack: the need for rapid, flexible experimentation versus the need for rigorous security. Notebooks are designed for agility, but when that agility includes an unauthenticated shell, it creates a massive liability.
The fact that a “methodical operator” was able to move from discovery to credential theft in under 10 hours suggests that attackers are now monitoring security advisories in real-time, treating the developer’s own documentation as a blueprint for the attack.
The next critical checkpoint for the community will be the analysis of how many organizations were actually breached before the patch was applied, as more telemetry data becomes available from security vendors. For now, the directive is simple: update, rotate, and restrict.
Do you use Marimo or similar notebook environments in your workflow? Share your thoughts on how to balance developer speed with security in the comments below.

