A critical security flaw in a widely used third-party Android software development kit (SDK) has left over 50 million users potentially exposed to data theft, with a disproportionate impact on the cryptocurrency sector. The vulnerability, found in the EngageLab SDK, could have allowed malicious applications on a single device to bypass the Android security sandbox and harvest private data from other installed apps.
The scale of the exposure is significant: more than 30 million installations of cryptocurrency and digital wallet apps were affected. When including non-wallet applications that integrated the same SDK, the total number of exposed installations surpasses 50 million.
The flaw was detailed in a report released April 9, 2026, by the Microsoft Defender Security Research Team. According to the researchers, the vulnerability allows a malicious app to leverage the trusted context of a vulnerable app to gain unauthorized access to protected components or internal directories.
The Mechanics of Intent Redirection
To understand how the EngageLab SDK flaw worked, one must look at how Android handles “Intents.” In the Android ecosystem, intents are messaging objects used to request an action from another app component. They act as the glue that allows different apps to communicate and share functionality.
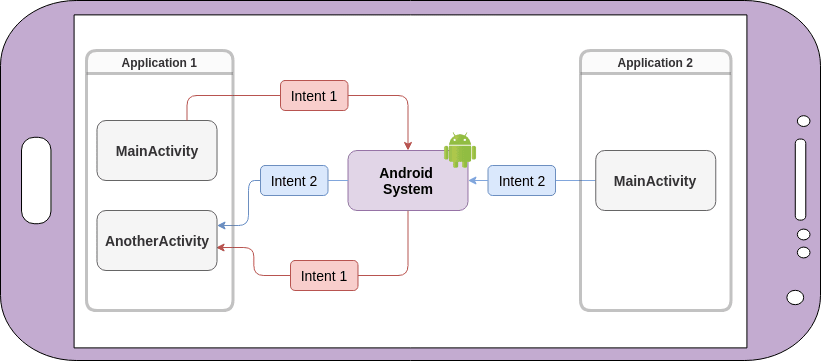
The specific issue identified in version 4.5.4 of the SDK is known as an intent redirection vulnerability. This occurs when an app sends an intent that can be manipulated by an external party. By taking advantage of the vulnerable app’s permissions—its “trusted context”—an attacker can redirect that intent to access private data or escalate privileges within the Android environment.
In a practical attack scenario, a user might unknowingly install a malicious app from an unofficial source. That malicious app could then exploit the EngageLab SDK flaw in a legitimate wallet app installed on the same device, effectively “jumping” the security sandbox to read the wallet’s internal directories and steal sensitive information.
A Supply Chain Risk for Digital Assets
The EngageLab SDK is primarily used for push notification services, designed to support developers deliver personalized, real-time engagement based on user behavior. Because these tools are designed for ease of integration, they often turn into “opaque” dependencies—pieces of code that developers drop into their apps without fully auditing the underlying security architecture.
This specific case highlights the fragility of the mobile supply chain, particularly for high-value targets like digital asset management. Microsoft noted that “this case shows how weaknesses in third‑party SDKs can have large‑scale security implications, especially in high‑value sectors like digital asset management.”
The risk is compounded when integrations expose exported components or rely on trust assumptions that are not validated across app boundaries. For crypto wallet users, where a single leak of a private key or seed phrase can result in a total loss of funds, these technical oversights carry immense financial stakes.
Timeline of Disclosure and Remediation
| Date | Event |
|---|---|
| April 2025 | Responsible disclosure of the vulnerability to EngageLab. |
| November 2025 | EngageLab releases version 5.2.1 to patch the flaw. |
| April 9, 2026 | Microsoft Defender Security Research Team publishes full report. |
Current Status and Next Steps for Users
Despite the severity of the potential exploit, Microsoft stated there is currently no evidence that the vulnerability was ever exploited in a malicious, real-world context. This suggests that the flaw was discovered and patched before bad actors could weaponize it on a mass scale.
Google has already taken action to mitigate the risk. Microsoft reported that all detected apps using the vulnerable versions of the SDK have been removed from the Google Play Store. This ensures that novel users cannot download affected versions and prompts existing developers to push updates.
For developers still utilizing the SDK, the directive is clear: update to version 5.2.1 or later immediately. Even seemingly trivial flaws in upstream libraries can have cascading impacts across millions of devices, making the update process a critical security requirement rather than a routine maintenance task.
Disclaimer: This article is for informational purposes only and does not constitute financial or legal advice regarding the management of digital assets.
The industry is now looking toward more rigorous auditing of third-party libraries to prevent similar “blind spot” vulnerabilities. The next major checkpoint for mobile security enthusiasts will be the upcoming Android security bulletins, which may provide further guidance on hardening intent filters against redirection attacks.
Do you use third-party SDKs in your development workflow? Share your thoughts on supply chain security in the comments below.

