The FBI confirmed Friday that the personal email account of Director Kash Patel was breached by a hacking group with ties to Iran, known as Handala. The group published photos and documents allegedly obtained from the account, prompting an investigation and raising concerns about potential exposure of personal information. Whereas the FBI stated the compromised data was historical and did not include government information, the incident underscores the growing threat of cyberattacks targeting high-profile individuals.
Handala announced the breach on one of its websites, claiming to have compromised “the so-called ‘impenetrable’ systems of the FBI” within hours. This action, the group stated, was in direct response to the FBI’s recent seizure of Handala domains and the U.S. Department of State’s offer of a reward of up to $10 million for information leading to the identification of the group’s members. The reward was announced as part of a broader effort to disrupt Iranian cyber-enabled psychological operations, according to a Justice Department press release.
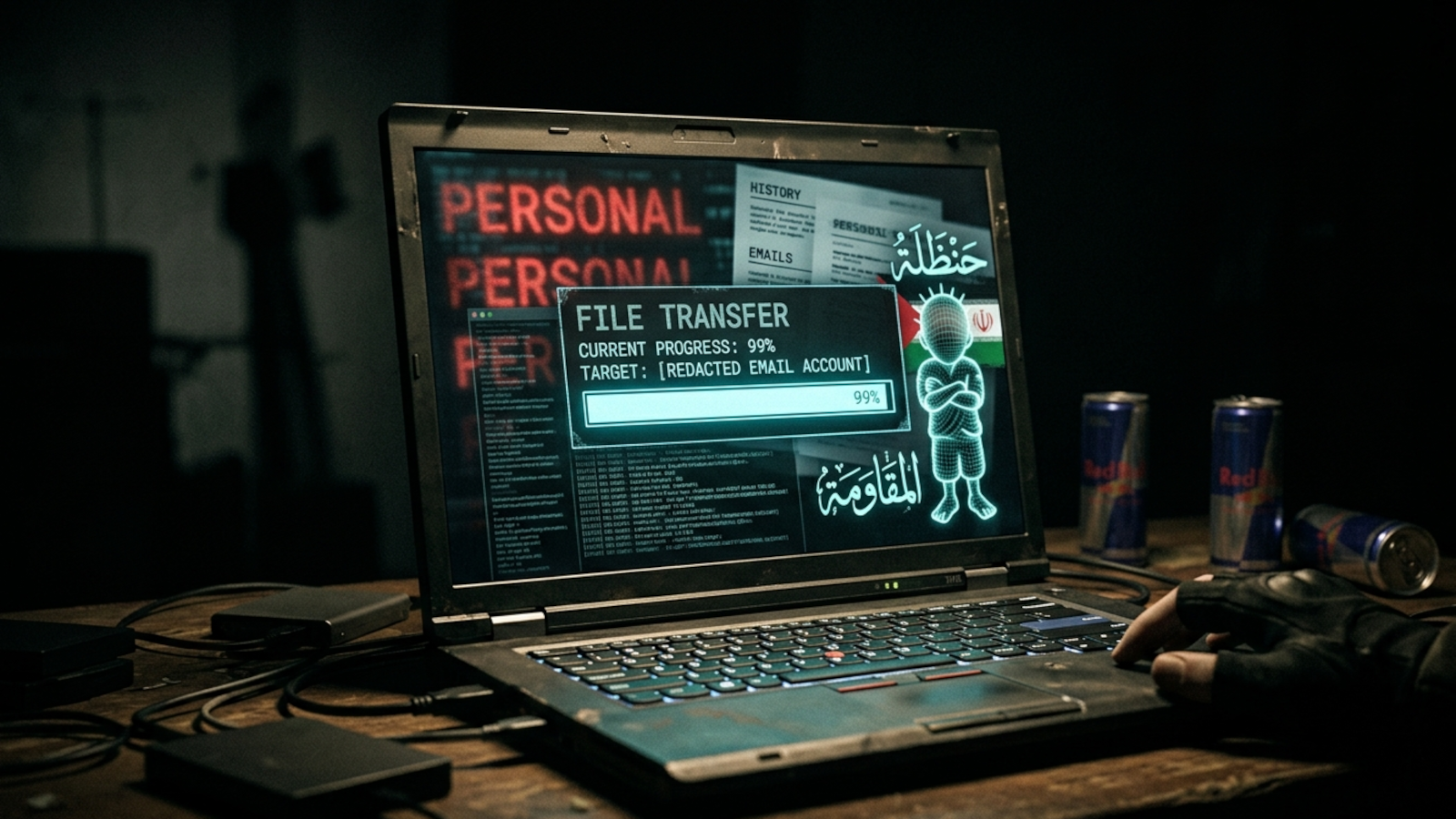
The hackers specifically targeted Patel’s personal Gmail inbox, according to BleepingComputer, and claimed to have access to “all personal and confidential information,” including emails, conversations, documents, and even allegedly classified files. Shortly after the announcement, Handala published watermarked personal photos and documents extracted from the inbox, along with email correspondence predating Patel’s tenure as FBI Director. A screenshot of the hackers’ announcement, posted by BleepingComputer, shows a boastful claim of success against a key U.S. Security official.
source: BleepingComputer
In a statement provided to BleepingComputer, the FBI acknowledged the targeting of Director Patel’s personal email information. “The FBI is aware of malicious actors targeting Director Patel’s personal email information, and we have taken all necessary steps to mitigate potential risks associated with this activity,” the statement read. “The information in question is historical in nature and involves no government information.” This confirmation aims to reassure the public that sensitive national security data was not compromised in the breach.
Who is Handala Hack?
Handala Hack, too known as Hatef and Hamsa, emerged in December 2023 and is identified as a hacktivist persona operating on behalf of Iran’s Ministry of Intelligence and Security (MOIS), according to research from Unit 42, a part of Palo Alto Networks. Their report details a pattern of cyber activity linked to the Iranian government, focusing on disruption and psychological operations. Prior to targeting Patel, the group gained notoriety for a significant breach of medical technology giant Stryker, where they wiped nearly 80,000 devices in a disruptive attack.
The group’s tactics often involve exploiting vulnerabilities in Microsoft environments, as demonstrated in the Stryker incident. This latest attack on Patel’s personal email highlights a shift towards targeting individuals connected to U.S. National security, potentially as a form of retaliation for U.S. Cyber operations against Iranian entities. The Department of Justice has been actively working to disrupt these Iranian cyber activities, as evidenced by the recent reward offer and domain seizures.
The Broader Context of Iranian Cyber Activity
The incident involving Director Patel’s email is part of a larger trend of increased cyber activity originating from Iran. The U.S. Government has repeatedly accused Iran of sponsoring cyberattacks targeting critical infrastructure, government agencies, and private companies. These attacks range from data theft and ransomware deployments to disruptive attacks aimed at causing economic damage and undermining public trust. The $10 million reward offered by the Department of State’s Rewards for Justice program underscores the seriousness with which the U.S. Government views the threat posed by Handala and other Iranian cyber groups.
Experts in cybersecurity emphasize the importance of strong email security practices, even for personal accounts. Multi-factor authentication, strong passwords, and vigilance against phishing attempts are crucial steps in protecting against unauthorized access. Though, even with these measures in place, high-profile individuals remain attractive targets for sophisticated hacking groups like Handala.
What Happens Next?
The FBI is continuing its investigation into the breach of Director Patel’s email account. While the agency maintains that no government information was compromised, the incident is likely to prompt a review of security protocols for high-ranking officials. The Department of Justice is also actively pursuing leads related to the Handala Hack Team, hoping to identify and prosecute the individuals responsible for the attacks. The ongoing reward offer remains in effect, encouraging anyone with information about the group to come forward.
The U.S. Government is expected to continue its efforts to counter Iranian cyber activity, employing a combination of defensive measures, law enforcement actions, and international cooperation. The incident involving Director Patel serves as a stark reminder of the persistent and evolving threat posed by state-sponsored hacking groups and the need for constant vigilance in the digital realm. The FBI has not provided a timeline for the completion of its investigation, but officials have stated they will provide updates as appropriate.
If you are concerned about your own online security, the Cybersecurity and Infrastructure Security Agency (CISA) offers resources and guidance on protecting yourself from cyber threats. You can find more information on their website: https://www.cisa.gov/
This is a developing story. We will continue to update this article as more information becomes available.