The promise of “cloning” a WhatsApp account is a recurring theme in the mobile app ecosystem, often appearing as enticing downloads on the Google Play Store. For many users, the desire to access a single account across multiple devices or to manage two separate numbers on one phone drives them to search for tools like como clonar whatsapp gratis. However, as a former software engineer, I have seen how these promises often mask significant security vulnerabilities and violations of service terms.
In the current landscape of mobile security, “cloning” typically refers to one of two things: the legitimate use of multi-account features or the illicit attempt to mirror someone else’s messages. While the former is a productivity tool, the latter is a breach of privacy that often leads users toward “spyware” or “trojans” disguised as utility apps. The risks associated with downloading unverified third-party APKs or Play Store apps claiming to offer “free cloning” are substantial, ranging from data theft to complete account takeover.
WhatsApp, owned by Meta, employs conclude-to-end encryption to ensure that only the sender and receiver can read messages. This architecture makes true “cloning” of a live session nearly impossible without physical access to the device or the compromise of the account’s registration SMS code. Most apps claiming to perform this action “gratis” (for free) are either simple wrappers for the official WhatsApp Web interface or, more dangerously, phishing tools designed to harvest user credentials.
The Technical Reality of Account Mirroring
To understand why “cloning” apps are often misleading, it is necessary to distinguish between app duplication and account mirroring. App duplication, often called “Parallel Space” or “Dual Apps,” is a legitimate Android feature that allows a user to install two separate instances of the same application. This allows a person to use two different phone numbers on one device—one for work and one for personal use—without actually “cloning” an existing account.
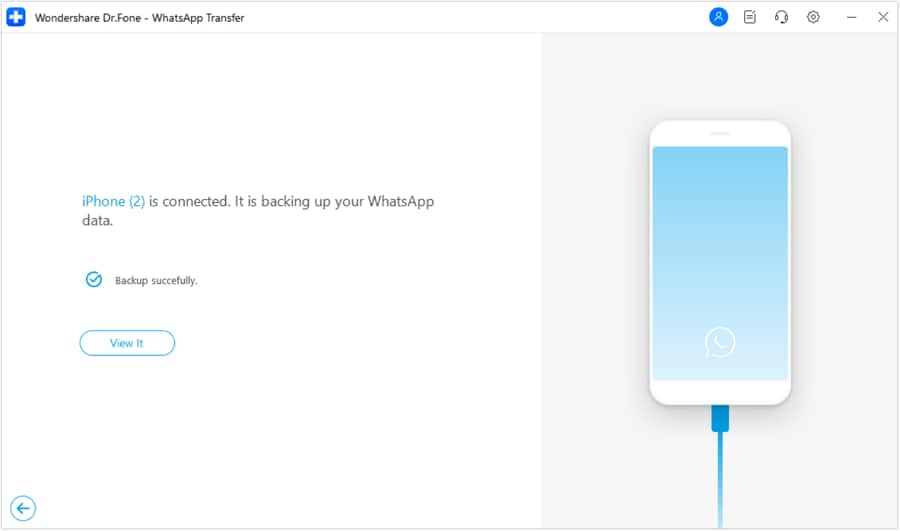
Account mirroring, however, is the process of gaining access to an existing account on a second device. The only official, secure method to achieve This represents through the WhatsApp Linked Devices feature. This allows a primary phone to link up to four companion devices (such as a laptop or tablet) via a QR code scan. Any app claiming to bypass this official handshake process is likely operating outside of WhatsApp’s security protocols.
When users encounter apps on the Google Play Store with titles like “como clonar whatsapp gratis,” they are often encountering “grey-ware.” These apps may initially appear functional but frequently request excessive permissions—such as access to contacts, microphones, and SMS logs—which are not required for the stated purpose of the app. This is a classic hallmark of data-harvesting software.
Comparing Official vs. Unofficial Methods
| Method | Mechanism | Security Level | Risk Factor |
|---|---|---|---|
| Linked Devices | Official QR Pairing | High (Encrypted) | None |
| App Cloners | Sandboxed Instance | Medium | Battery/RAM Drain |
| Third-Party “Cloners” | Credential Harvesting | Low/Dangerous | Account Theft/Malware |
Identifying the Red Flags of “Free” Cloning Apps
The allure of a free tool often blinds users to the technical red flags. In the software world, “free” often means the user’s data is the product. Apps that promise to “clone” WhatsApp without the target’s knowledge often employ social engineering tactics to trick the user into granting administrative privileges on their Android device.

One common tactic is the “overlay attack,” where a malicious app creates a transparent layer over the legitimate WhatsApp login screen. When the user enters their phone number or verification code, the malicious app captures the keystrokes and sends them to a remote server. This allows an attacker to register the account on their own device, effectively locking the original owner out of their account.
many of these apps are designed to bypass the Google Play Protect scanning process by using obfuscated code. While Google regularly removes malicious apps, the speed at which new “cloner” apps are uploaded often creates a window of vulnerability for unsuspecting users.
Protecting Your Privacy and Account Integrity
The most effective way to prevent unauthorized cloning of your own account is to enable Two-Step Verification. This adds a personal PIN to your account, meaning that even if someone manages to steal your SMS verification code, they cannot access your messages without the secondary PIN. This is the single most important line of defense against the tools marketed as “como clonar whatsapp gratis.”
Users should also regularly audit their “Linked Devices” list within the WhatsApp settings. If an unfamiliar device appears in the list, it should be logged out immediately. This ensures that any “cloned” session—whether created legitimately or through a security lapse—is terminated instantly.
For those seeking to manage multiple accounts, the safest path is to use the official “Multi-Account” feature recently rolled out by WhatsApp, which allows users to add a second account within the same app without needing third-party cloning software. This eliminates the necessitate for risky downloads and keeps all data within the encrypted ecosystem.
As Meta continues to update its security architecture, the window for third-party “cloning” tools to operate is closing. The next major security checkpoint for users will be the wider rollout of “Passkeys,” which aims to replace SMS-based verification with biometric authentication, further neutralizing the effectiveness of phishing-based cloning apps.
If you have encountered these types of apps or have questions about securing your digital footprint, we invite you to share your experiences in the comments below.