Rockstar Games is once again facing a security crisis as a hacking collective threatens to leak a massive cache of internal data. The group, known as ShinyHunters, has issued a ransom demand to the Grand Theft Auto developer, claiming they have successfully breached the company’s systems and are holding a significant volume of files hostage.
The incident, which reportedly occurred on a Saturday, highlights the ongoing vulnerability of high-profile gaming studios to targeted cyberattacks. The hackers claim they gained entry through Anodot, a third-party cloud server service, utilizing the same “supply chain” vulnerability that has plagued other major tech firms in recent years. This method of entry—targeting a vendor rather than the primary target’s own perimeter—is a common tactic used to bypass robust internal security.
In a statement regarding the Rockstar offer for utpressing etter nytt datainnbrudd, the company confirmed that a breach did occur but sought to downplay the severity of the event. Rockstar stated that some “insignificant information” about the company was compromised via a third party and asserted that the incident would have no impact on their organization or their players.
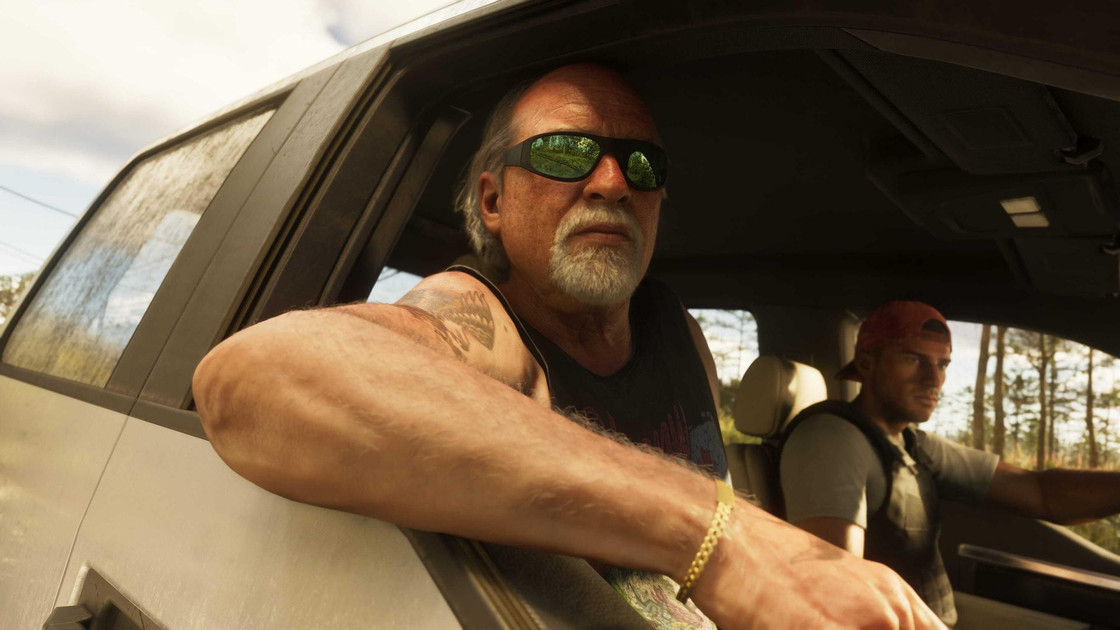
The stakes for this specific breach are exceptionally high due to the anticipation surrounding the studio’s next major release. The gaming industry is currently awaiting the launch of Grand Theft Auto VI, a project that has become a primary target for digital thieves seeking high-value intellectual property to leverage for profit.
Rockstar
The Anatomy of the Attack and the Ransom Deadline
The group ShinyHunters has a documented history of targeting high-profile platforms, often specializing in the theft of sensitive data and the subsequent sale or leak of that information. In this instance, the group has set a strict timeline for the studio. According to the hackers, if their ransom demands are not met by Tuesday, they intend to publish the stolen files to the public domain.
Whereas the exact nature of the stolen data remains unconfirmed, the threat of a “massive” leak has position the industry on edge. In the world of game development, “massive” could range from internal emails and financial documents to early builds of software and concept art. For Rockstar, the primary concern is the potential exposure of assets related to GTA VI, which would disrupt the carefully managed marketing rollout of the title.
From a technical perspective, the alleged use of Anodot as an entry point suggests a failure in the security posture of a third-party partner. As a former software engineer, I’ve seen this pattern repeatedly: a company spends millions on its own “fortress” security, only to be breached because a smaller vendor with fewer resources had a misconfigured API or an unpatched server. This “weakest link” phenomenon is currently one of the greatest challenges in cybersecurity management.
A History of High-Stakes Leaks
This is not the first time Rockstar has dealt with a breach of this magnitude. The company’s struggle with data security became a global headline in 2022, when a catastrophic leak of GTA VI footage occurred. That incident saw over 90 videos and numerous images surface online, providing the public with an unprecedented look at the game’s mechanics, including the revelation that the story would feature two playable protagonists.
The 2022 breach was particularly damaging because it was not just a data theft but a public relations nightmare. The footage was spread across social media platforms within hours, forcing the company to deal with the fallout of its most anticipated project being partially spoiled years before release. That specific case eventually led to the arrest of a teenager who was allegedly involved in the breach and the subsequent extortion attempts.
| Year | Event | Outcome |
|---|---|---|
| 2022 | Massive GTA VI leak | 90+ videos leaked; perpetrator arrested |
| Recent | ShinyHunters Breach | Ransom demand; breach via third-party (Anodot) |
What This Means for Players and the Industry
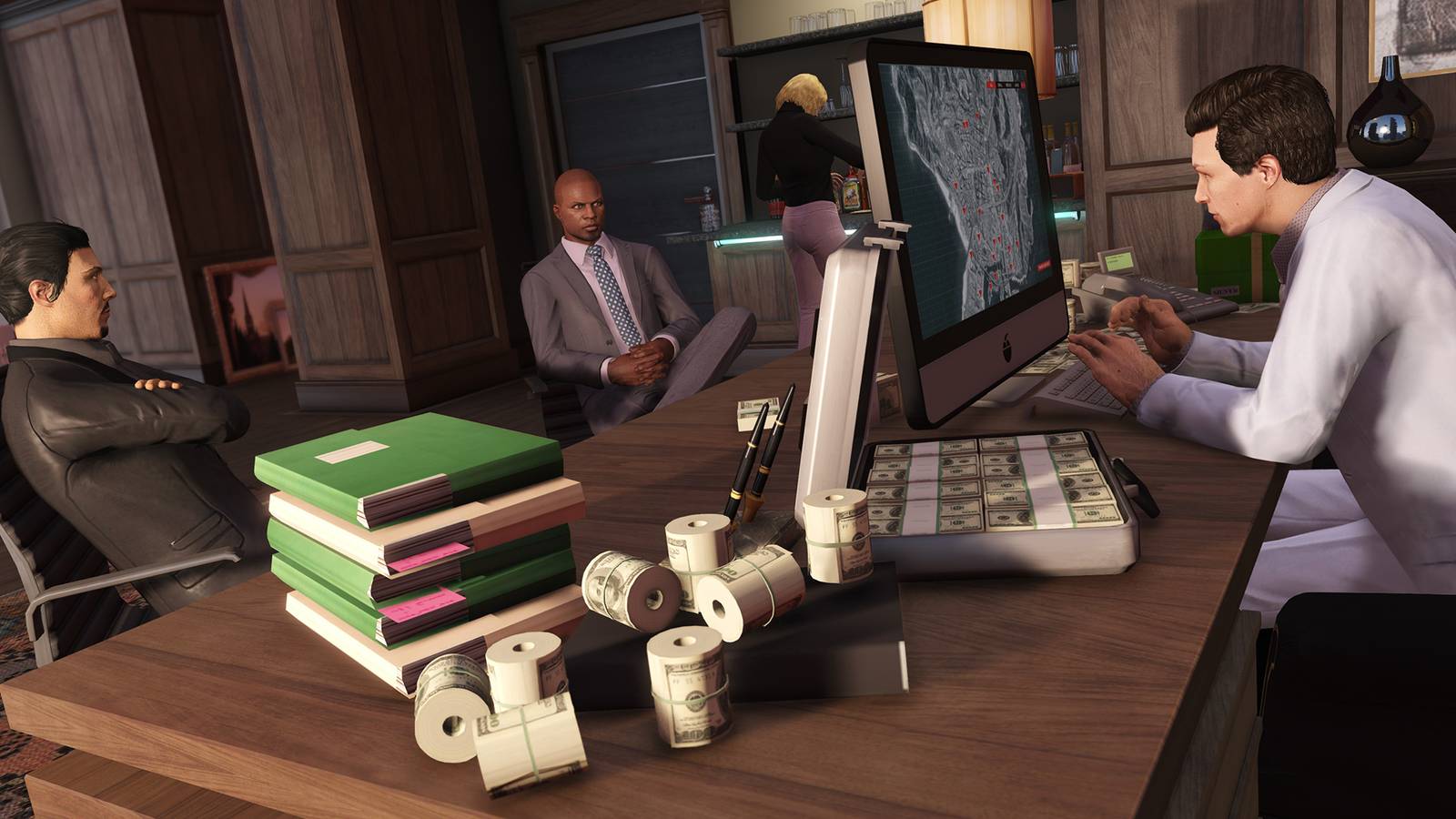
For the average gamer, the immediate impact of this breach appears minimal. Rockstar’s insistence that the event has “no significance” for its players suggests that user passwords, credit card details, and personal account information were not the primary targets. The focus of this attack seems to be corporate espionage and financial extortion rather than a wide-scale consumer data theft.
However, the broader implication for the gaming industry is a sobering reminder of the “spoiler economy.” As games become more complex and development cycles longer, the value of leaked information increases. Hackers are no longer just looking for credit card numbers; they are looking for intellectual property that can be used to shake down multi-billion dollar corporations.
The industry’s reliance on cloud-based third-party services for analytics and server management—like the service mentioned in this breach—creates a sprawling attack surface. When a developer uses a cloud service, they are essentially trusting that service’s security as much as their own. If that trust is misplaced, the results are exactly what we are seeing now: a public ransom demand and the threat of intellectual property loss.
Next Steps and Official Monitoring
The immediate focus now shifts to the Tuesday deadline set by ShinyHunters. Whether Rockstar chooses to negotiate, ignore the threat, or pursue legal action through federal law enforcement will determine if more data surfaces in the coming days. The company has not indicated any change in the development timeline for its upcoming titles, suggesting that the core production pipeline remains intact despite the breach.
We will continue to monitor official channels for updates regarding the status of the stolen data and any further statements from the company. For the latest verified information, users are encouraged to follow the official Rockstar Games news feed.
Do you feel gaming companies are doing enough to secure their intellectual property against these high-profile leaks? Share your thoughts in the comments below.