A sophisticated, state-sponsored hacking group has infiltrated dozens of government and critical infrastructure networks across 37 countries, launching what researchers are calling ‘Shadow Campaigns.’ The widespread espionage operation, which began as early as January 2024, has raised alarms about the escalating threat to global cybersecurity.
Global Espionage Network Uncovered
Table of Contents
Researchers have identified a highly coordinated effort to compromise sensitive data from governments worldwide.
- The threat actor, tracked as TGR-STA-1030/UNC6619, is believed to operate from Asia.
- ‘Shadow Campaigns’ targeted government ministries, law enforcement, and critical infrastructure sectors.
- The group exploited known vulnerabilities and utilized custom malware, including a new Linux rootkit dubbed ‘ShadowGuard.’
- Reconnaissance activity spiked during the U.S. government shutdown in October 2025, focusing on the Americas.
Between November and December 2025, the group also conducted extensive reconnaissance, scanning government entities in a staggering 155 countries, according to Unit 42 at Palo Alto Networks. This broad targeting suggests a deliberate attempt to map global networks and identify potential vulnerabilities.
What makes this attack unique? The scale and persistence of ‘Shadow Campaigns’ set it apart, with successful compromises confirmed in at least 70 organizations. The actor’s toolkit is extensive, and their methods demonstrate a high level of operational maturity.
Targets Span the Globe
The attacks weren’t random. ‘Shadow Campaigns’ activity primarily focused on government ministries, law enforcement agencies, border control, financial institutions, trade organizations, energy and mining companies, immigration services, and diplomatic agencies. Confirmed compromises include organizations involved in trade policy, geopolitical issues, and elections in the Americas, as well as ministries and parliaments across Europe. Australia’s Treasury Department and government infrastructure in Taiwan were also affected.
Source: Unit 42
The timing of reconnaissance activity appeared to be strategically linked to specific events. During the U.S. government shutdown in October 2025, the threat actor increased scanning of entities across North, Central, and South America, including Brazil, Canada, Dominican Republic, Guatemala, Honduras, Jamaica, Mexico, Panama, and Trinidad and Tobago. Just 30 days before Honduras’ national election, researchers discovered reconnaissance against at least 200 IP addresses hosting Honduran government infrastructure, coinciding with both candidates’ stated willingness to restore diplomatic ties with Taiwan.
Compromised Entities
Unit 42 identified several specific organizations compromised by TGR-STA-1030/UNC6619, including:
- Brazil’s Ministry of Mines and Energy
- The network of a Bolivian entity associated with mining
- Two of Mexico’s ministries
- A government infrastructure in Panama
- An IP address geolocating to a Venezolana de Industria Tecnológica facility
- Compromised government entities in Cyprus, Czechia, Germany, Greece, Italy, Poland, Portugal, and Serbia
- An Indonesian airline
- Multiple Malaysian government departments and ministries
- A Mongolian law enforcement entity
- A major supplier in Taiwan’s power equipment industry
- A Thai government department (likely focused on economic and international trade information)
- Critical infrastructure entities in the Democratic Republic of the Congo, Djibouti, Ethiopia, Namibia, Niger, Nigeria, and Zambia
The group also attempted to connect via SSH to Australia’s Treasury Department, Afghanistan’s Ministry of Finance, and Nepal’s Office of the Prime Minister and Council of Ministers.
Attack Methods and Tools
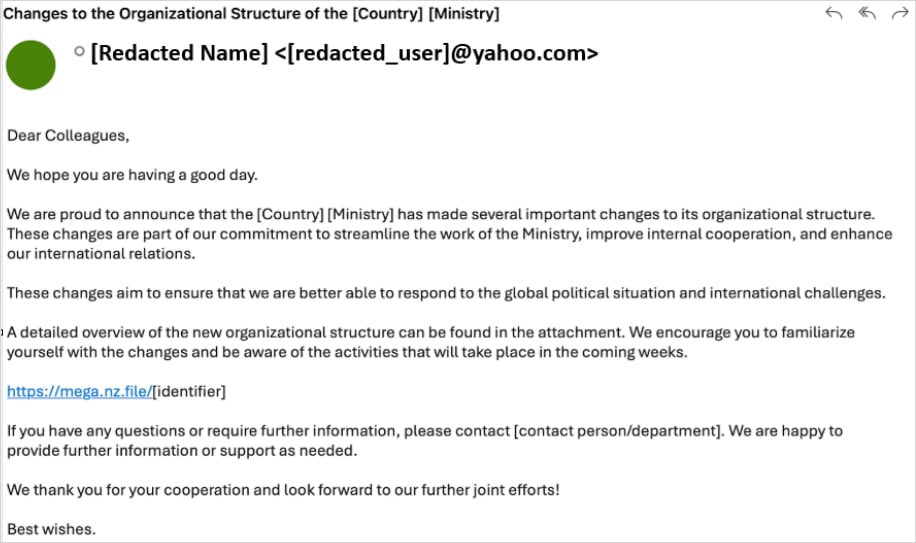
The initial stages of ‘Shadow Campaigns’ relied on highly targeted phishing emails, often disguised as internal ministry reorganization announcements. These emails contained links to malicious archives hosted on Mega.nz, which delivered a malware loader called Diaoyu and a zero-byte PNG file named pic1.png. The Diaoyu loader, under certain conditions, would then fetch Cobalt Strike payloads and the VShell framework for command-and-control (C2).
Source: Unit 42
Researchers discovered that Diaoyu included checks to evade analysis, requiring a horizontal screen resolution of at least 1440 pixels and verifying the presence of the pic1.png file. The loader also scanned for running security products, including Kaspersky, Avira, Bitdefender, Sentinel One, and Norton (Symantec). Beyond phishing, the group exploited at least 15 known vulnerabilities in software like SAP Solution Manager, Microsoft Exchange Server, D-Link, and Microsoft Windows.
Introducing ShadowGuard
Adding to the complexity, TGR-STA-1030/UNC6619 deployed a custom Linux kernel eBPF rootkit called ‘ShadowGuard.’ Researchers describe eBPF backdoors as particularly difficult to detect because they operate within the kernel space, allowing manipulation of system functions and audit logs before security tools can intervene. ShadowGuard conceals malicious processes, hides up to 32 PIDs, and can obscure files and directories named swsecret, while also allowing operators to define processes that should remain visible.
The group’s infrastructure utilized legitimate VPS providers in the U.S., Singapore, and the UK, along with relay servers and residential proxies or Tor for traffic obfuscation. They also employed C2 domains designed to appear familiar to targets, such as using .gouv top-level extensions for French-speaking countries and dog3rj[.]tech in European attacks.
Unit 42 assesses that TGR-STA-1030/UNC6619 is an operationally mature espionage actor prioritizing strategic, economic, and political intelligence, with a significant impact already felt across numerous governments worldwide. The researchers have released indicators of compromise (IoCs) to aid in detection and prevention efforts.
