Cybersecurity researchers have identified a high-velocity threat actor, tracked as Storm-1175, that is specializing in a race against the clock. The group focuses its gaze on vulnerable web-facing assets, exploiting the critical window of time between when a software vulnerability is publicly disclosed and when organizations actually apply the necessary patches.
Operating with an aggressive operational tempo, Storm-1175 leverages these “N-day” vulnerabilities to gain initial entry into corporate networks. Once inside, the group moves with startling speed; in some instances, the transition from initial access to full-scale data exfiltration and the deployment of Medusa ransomware occurs within 24 hours. In most cases, the entire attack chain is completed within a few days.
The impact of these high-tempo Medusa ransomware operations has been felt across several critical sectors, including healthcare, finance, professional services, and education. Intrusions have been documented in the United States, the United Kingdom, and Australia, highlighting a broad geographic reach and a preference for organizations that may struggle to patch perimeter systems instantaneously.
As a former software engineer, I find the group’s proficiency in “exploit chaining” particularly concerning. Rather than relying on a single flaw, Storm-1175 often links multiple vulnerabilities together to escalate privileges or achieve remote code execution (RCE). This methodical approach allows them to bypass layered defenses and establish a deep foothold before security teams even realize the perimeter has been breached.
The Mechanics of Rapid Exploitation
The core of Storm-1175’s success is its ability to weaponize new vulnerabilities almost immediately after they are announced. Since 2023, Microsoft Threat Intelligence has observed the group exploiting more than 16 different vulnerabilities. This rapid rotation of exploits ensures they always have a working key for a variety of “locked” doors across the internet.
A stark example of this speed occurred with CVE-2025-31324, which affected SAP NetWeaver. The security flaw was disclosed on April 24, 2025; by April 25, Storm-1175 was already exploiting it in the wild. This 24-hour turnaround leaves virtually no room for manual patching cycles in large enterprises.
While N-days are their primary tool, the group has evolved. Researchers have identified at least three zero-day vulnerabilities used by the actor, including CVE-2026-23760 in SmarterMail and CVE-2025-10035 in GoAnywhere Managed File Transfer. In both cases, the group exploited the flaws a full week before they were publicly disclosed, suggesting either an advanced internal development capability or the utilize of professional exploit brokers.
The group is not limited to Windows environments. In late 2024, they were observed targeting vulnerable Oracle WebLogic instances on Linux systems, demonstrating a cross-platform capability that expands their potential target list.
Lateral Movement and the Abuse of IT Tools
Once the initial breach is achieved—often via a web shell or a remote access payload—Storm-1175 focuses on persistence. They typically create new user accounts and immediately elevate them to administrator status to ensure they cannot be easily locked out of the system.
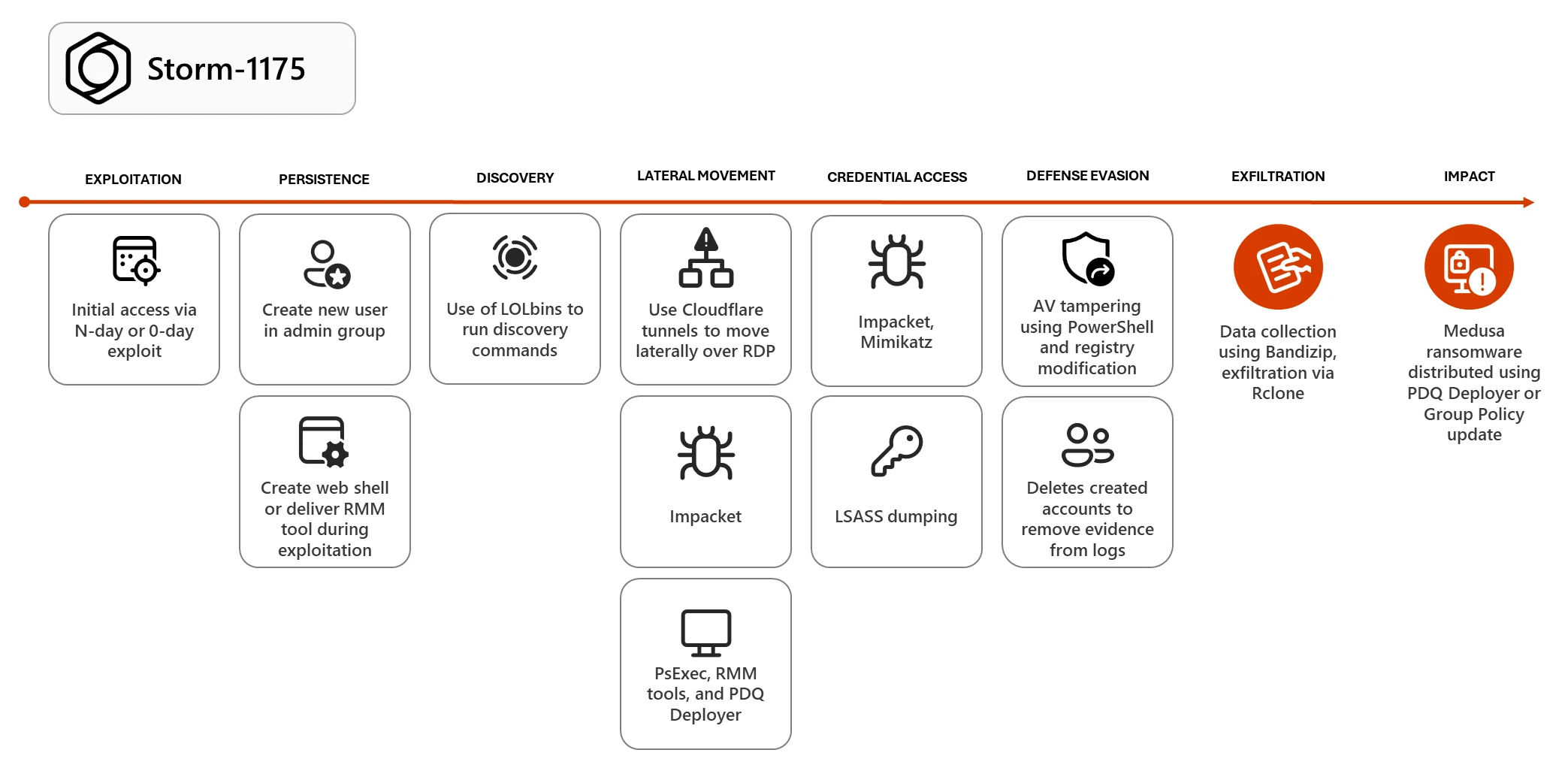
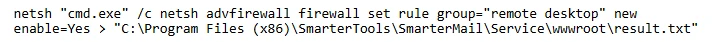
To move through the network, the group employs a “living-off-the-land” strategy, using legitimate system binaries like PowerShell and PsExec to avoid detection. They have also been seen using Cloudflare tunnels, cleverly renamed to mimic legitimate system files like conhost.exe, to facilitate Remote Desktop Protocol (RDP) movement. If RDP is disabled by a company’s security policy, the attackers simply use their administrative privileges to rewrite the Windows Firewall rules and open the port themselves.
Perhaps most dangerously, Storm-1175 heavily relies on Remote Monitoring and Management (RMM) tools. By deploying software like AnyDesk, ConnectWise ScreenConnect, or Atera, they essentially install their own “backdoor” that looks like legitimate IT support activity. They also leverage PDQ Deployer, a tool designed for system administrators to install software silently, to push the final Medusa ransomware payloads across the entire network simultaneously.
Credential Theft and Security Sabotage
The group’s path to the “crown jewels”—the Domain Controller—usually involves aggressive credential harvesting. They use Impacket and Mimikatz to dump passwords from the Local Security Authority Subsystem Service (LSASS). In some cases, they have even used scripts to recover passwords from Veeam backup software, which allows them to pivot to remote hosts that were previously disconnected.
Before deploying the ransomware, Storm-1175 systematically disables security software. They modify the Windows registry to tamper with Microsoft Defender Antivirus and use encoded PowerShell commands to add the entire C: drive to the antivirus exclusion list. This effectively blinds the organization’s security tools, allowing the ransomware to execute without triggering alerts.
The Final Phase: Double Extortion
Storm-1175 utilizes the Medusa ransomware model, which is based on a “Ransomware-as-a-Service” (RaaS) structure. This involves a double extortion tactic: the attackers encrypt the victim’s data and simultaneously steal sensitive files to a remote cloud resource using tools like Rclone, and Bandizip.
The stolen data is then held hostage on a dedicated leak site. If the victim refuses to pay for the decryption key, the group threatens to publish the private data publicly. This pressure tactic is designed to force payment even from organizations that have robust offline backups and can technically recover their systems without a key.
| Attack Stage | Primary Tool/Method | Purpose |
|---|---|---|
| Initial Access | N-Day/Zero-Day Exploits | Perimeter breach via web-facing assets |
| Persistence | RMM Tools (e.g., AnyDesk) | Maintaining covert access |
| Lateral Movement | PDQ Deployer / PsExec | Spreading across the network |
| Exfiltration | Rclone / Bandizip | Stealing data for double extortion |
| Impact | Medusa Ransomware | Data encryption and ransom demand |
To defend against these tactics, security professionals are encouraged to implement Credential Guard and enforce strict multi-factor authentication (MFA) on all RMM tools. Reducing the use of local administrator rights and employing external attack surface management tools can help organizations identify the same “exposed” assets that Storm-1175 is currently scanning for.
As the group continues to refine its ability to weaponize zero-day flaws, the window for patching is shrinking. The next critical checkpoint for defenders will be the monitoring of emerging vulnerabilities in managed file transfer (MFT) and mail server software, which have historically been the primary entry points for this actor.
Do you have experience defending against high-velocity ransomware? Share your thoughts and strategies in the comments below.

