A financially motivated cybercrime group is actively targeting organizations with a wiper attack specifically designed to impact systems in Iran, escalating tensions in the region’s already fraught digital landscape. The group, known as TeamPCP, is leveraging compromised cloud services and a self-propagating worm to erase data on systems configured with Iran’s time zone or using Farsi as the default language. This latest campaign represents a shift from data theft and extortion towards destructive activity, raising concerns about the group’s motivations and potential geopolitical implications.
The wiper campaign, which began over the weekend, follows months of activity by TeamPCP exploiting vulnerabilities in cloud infrastructure. Security researchers first observed the group in December 2025, compromising corporate cloud environments through exposed Docker APIs, Kubernetes clusters, Redis servers, and the React2Shell vulnerability. Their initial focus was on stealing authentication credentials and extorting victims via Telegram, but this recent development signals a more aggressive and potentially destabilizing tactic. The group’s ability to rapidly adapt and deploy new malicious payloads highlights the evolving threat landscape facing organizations reliant on cloud services.
A snippet of the malicious CanisterWorm that seeks out and destroys data on systems that match Iran’s timezone or have Farsi as the default language. Image: Aikido.dev.
TeamPCP’s Cloud-Native Approach
According to a January profile by the security firm Flare, TeamPCP distinguishes itself by focusing on exploiting exposed control planes – the management interfaces of cloud infrastructure – rather than directly targeting individual endpoints. This approach allows them to gain broad access and move laterally within compromised networks. Flare’s research indicates that Azure (61%) and Amazon Web Services (AWS) (36%) account for 97% of the servers compromised by the group. “TeamPCP’s strength does not come from novel exploits or original malware, but from the large-scale automation and integration of well-known attack techniques,” wrote Assaf Morag, a researcher at Flare. The firm describes the group as having “industrialized existing vulnerabilities, misconfigurations, and recycled tooling into a cloud-native exploitation platform that turns exposed infrastructure into a self-propagating criminal ecosystem.”
This strategy was recently demonstrated through a supply chain attack targeting Trivy, a vulnerability scanner developed by Aqua Security. On March 19, TeamPCP injected credential-stealing malware into official Trivy releases on GitHub Actions. Whereas Aqua Security has since removed the malicious files, Wiz, another security firm, reported that the attackers successfully published malicious versions capable of stealing SSH keys, cloud credentials, Kubernetes tokens, and cryptocurrency wallets from users.
The ‘CanisterWorm’ and Targeted Wiping
The infrastructure used in the Trivy attack was then repurposed to deploy the wiper payload targeting Iran. Charlie Eriksen, a security researcher at Aikido, identified the malicious code and detailed the attack in a blog post on Sunday. The wiper component, Eriksen explained, identifies systems based on their timezone and locale settings. If a system is determined to be in Iran and has access to a Kubernetes cluster, the wiper will destroy data on every node within that cluster. Otherwise, it will wipe the local machine. “If it doesn’t it will just wipe the local machine,” Eriksen told KrebsOnSecurity.
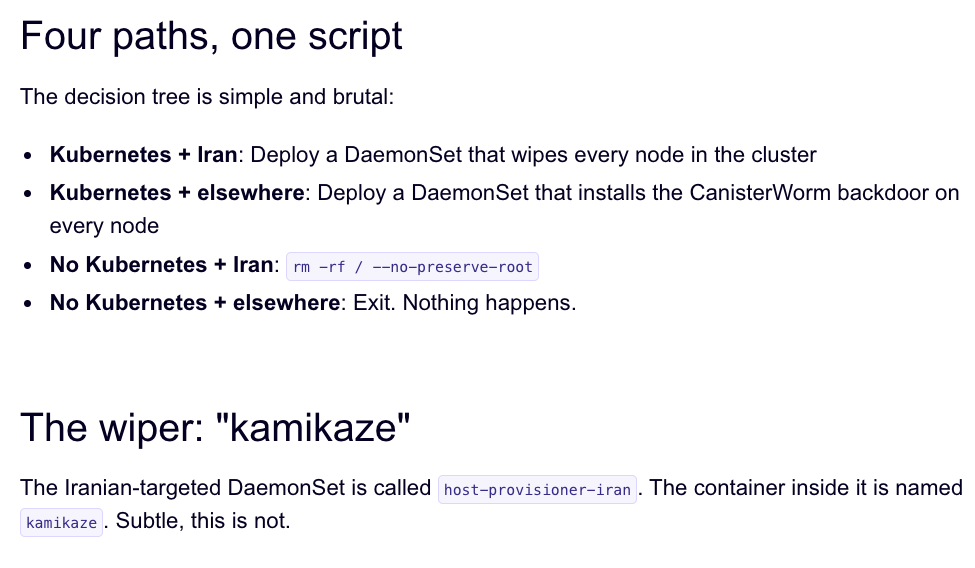
Image: Aikido.dev.
Aikido has dubbed TeamPCP’s infrastructure “CanisterWorm” due to its reliance on an Internet Computer Protocol (ICP) canister – a tamperproof, blockchain-based system for storing and executing code. This architecture makes the infrastructure resilient to takedown attempts, as the canisters remain accessible as long as the operators continue to pay the associated virtual currency fees.
Bragging Rights and Potential Motives
Eriksen reports that members of TeamPCP are openly discussing their exploits on a Telegram group, claiming to have stolen significant amounts of data from major companies, including a large multinational pharmaceutical firm. They reportedly used their access to spam GitHub accounts with junk messages, seemingly to demonstrate the extent of their compromise. Security experts believe this activity may be an attempt to maintain the visibility of their malicious packages in GitHub search results. Catalin Cimpanu, a reporter with Risky Business, wrote in a recent newsletter that attackers are increasingly manipulating GitHub search rankings to promote malicious code.
This latest incident marks the second major supply chain attack involving Trivy in as many months, following a previous compromise in February linked to a threat known as HackerBot-Claw. Eriksen believes TeamPCP leveraged access gained during the initial Trivy attack to launch the wiper campaign. However, he notes that it’s currently unclear whether the wiper successfully destroyed data on any systems, as the malicious payload was only active for a limited time.
“They’ve been taking [the malicious code] up and down, rapidly changing it adding new features,” Eriksen said, adding that when the canister wasn’t distributing malware, it redirected visitors to a Rick Roll video on YouTube. “It’s a little all over the place, and there’s a chance this whole Iran thing is just their way of getting attention,” Eriksen said. “I feel like these people are really playing this Chaotic Evil role here.”
The increasing frequency of supply chain attacks underscores the growing sophistication of threat actors and the challenges facing organizations in securing their software supply chains. Cimpanu observed that these attacks are becoming more efficient, and GitHub’s security team will need to enhance its defenses to address the issue.
Update, 2:40 p.m. ET: Wiz is reporting that TeamPCP also pushed credential stealing malware to the KICS vulnerability scanner from Checkmarx, and that the scanner’s GitHub Action was compromised between 12:58 and 16:50 UTC today (March 23rd).
Looking Ahead
Security researchers are continuing to monitor TeamPCP’s activity and analyze the CanisterWorm infrastructure. Aqua Security and GitHub are working to mitigate the vulnerabilities exploited in the Trivy supply chain attacks. Organizations are urged to review their cloud security configurations, implement robust access controls, and monitor for suspicious activity. The next update from Wiz regarding the KICS vulnerability is expected within 24 hours, providing further insight into the scope of the latest compromise. This incident serves as a stark reminder of the evolving cyber threat landscape and the importance of proactive security measures.
Have thoughts on this story? Share your comments below, and please consider sharing this article with your network.

