A simple flashlight app or a tool promising to clear your phone’s memory may seem harmless, but for many users, these utilities are acting as Trojan horses for sophisticated data theft. Security analysts are warning of a surge in “invisible” malicious applications that bypass traditional scrutiny to infiltrate official app stores, quietly harvesting contacts, passwords, and sensitive banking credentials.
This trend represents a shift in cybercrime, moving away from complex hacking attempts toward exploiting human trust and haste. By masquerading as essential tools, these apps trick users into granting broad system permissions that effectively hand over the keys to their digital lives. If you have a utility app on your device that you rarely employ or that requests unusual access, you may be at risk of a data breach.
The danger is particularly acute because these programs often perform the basic function they advertise. A fake flashlight will indeed light up the LED, and a memory optimizer may show a simulated cleaning process. This “functional camouflage” ensures the user remains unaware that a hidden process is running in the background, transmitting private data to a remote server.
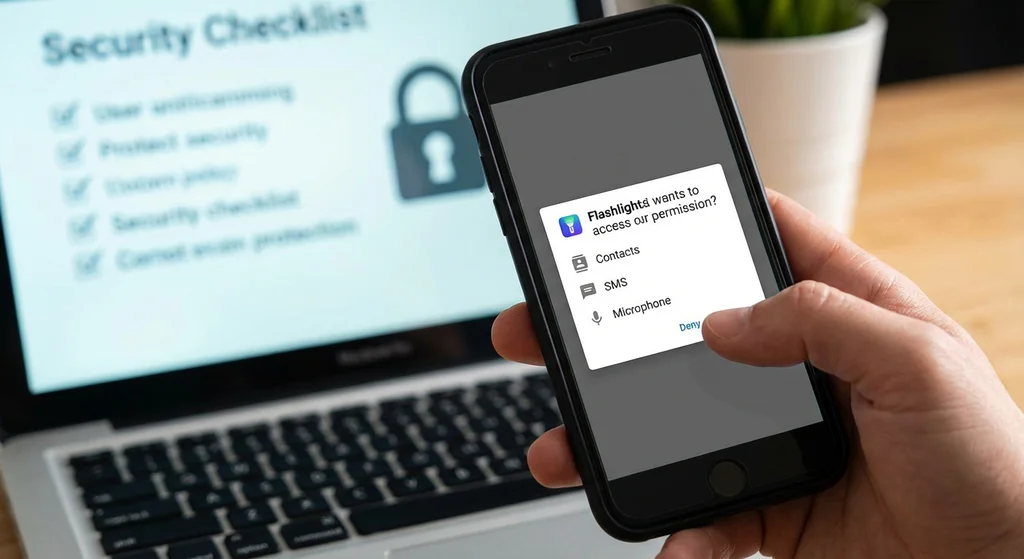
According to security researchers at ESET, these simple utilities have long been among the most common carriers of malicious code. The strategy is simple: target the user’s desire for a quick fix—like a faster phone or a brighter light—and leverage that impulse to secure permissions that no flashlight should ever need.
The Mechanics of the Stealth Attack
Modern mobile threats often utilize spyware—software designed specifically to spy on the device owner. One of the most dangerous tactics currently observed is the “delayed payload.” A security campaign highlighted by Check Point revealed that some applications are initially benign to pass app store screenings. Once installed, the app connects to a remote server to download the actual malicious code, transforming a harmless tool into a data-stealing engine.
Beyond simple data harvesting, attackers are increasingly targeting the “Accessibility Services” feature of mobile operating systems. Originally designed to assist users with disabilities by allowing software to read screen content and control the interface, this feature is now being weaponized. When a malicious app gains accessibility access, it can effectively “see” everything on the screen and even perform actions on the user’s behalf, such as confirming a fraudulent bank transfer without the user’s knowledge.
Once the spyware secures access to SMS messages and notifications, the attacker can intercept two-factor authentication (2FA) codes. This allows them to bypass security layers for social media accounts and online banking, often leaving the victim unaware of the breach until funds disappear or accounts are locked.
Why Detection is Difficult for the Average User
The National Cybersecurity Authority (NÚKZS) has noted a rise in attacks targeting general mobile users. These campaigns rely heavily on social engineering and the manipulation of app store metrics. Many of these fraudulent apps boast high ratings and thousands of downloads, but these figures are often fabricated through “review farms” or automated bots to create a false sense of legitimacy.
The psychological trap is the “permission gap.” When a user is prompted to allow an app to access their contacts or microphone, they often click “Allow” without thinking, especially if they are in a hurry. For a system cleaner or a flashlight, there is no technical reason to require access to SMS or the microphone, yet this is exactly what the spyware requires to function.
the risk is amplified by outdated software. Although manufacturers release security patches regularly, many users delay these updates. This leaves known vulnerabilities open, which malicious apps can exploit to escalate their privileges within the system, moving from a restricted “sandbox” to full control of the device.
Common Red Flags in Utility Apps
| App Type | Legitimate Need | Red Flag Permission |
|---|---|---|
| Flashlight | Camera/LED Access | SMS, Contacts, Microphone |
| Battery Optimizer | Battery Status | Call Logs, Accessibility Services |
| File Manager | Storage Access | SMS Read/Write, Contacts |
| Memory Cleaner | System Cache Access | Location, Full Screen Overlay |
Immediate Steps for Device Protection
To mitigate the risk of data theft, users should conduct a thorough audit of their installed applications. Focus on tools downloaded long ago or those whose purpose is no longer clear. If an app’s requested permissions do not align with its core function, it should be removed immediately.

The following steps are recommended for immediate security hardening:
- Audit Permissions: Navigate to your device settings and review which apps have access to “Sensitive Permissions” (SMS, Microphone, Contacts, Location).
- Uninstall Unused Utilities: Delete any third-party flashlights, “RAM boosters,” or “Battery savers,” as most modern smartphones have these functions built-in.
- Force System Updates: Install the latest OS security patches to close vulnerabilities that spyware uses to gain root access.
- Deploy Verified Security: Consider using a reputable mobile security suite that scans for known spyware signatures.
If you suspect that your data has already been compromised, the priority shifts to containment. Change passwords for your primary email, social media, and financial accounts immediately. For banking, enable advanced authentication methods, such as biometric confirmation (fingerprint or face ID) or a dedicated hardware token, to ensure that a stolen SMS code is not enough to authorize a transaction.
As smartphones increasingly serve as the central hub for our identity, financial assets, and private communications, they remain the primary target for cybercriminals. A small amount of vigilance during the installation process—specifically questioning why a simple app needs wide-ranging access—can prevent long-term identity theft and financial loss.
Security agencies continue to monitor the evolution of these “sleeper” apps. The next critical checkpoint for users will be the release of updated security guidelines from the National Cybersecurity Authority, which typically provides updated threat landscapes and specific app signatures to avoid.
Disclaimer: This article is for informational purposes only and does not constitute professional cybersecurity consulting.
Have you noticed any unusual battery drain or strange permissions requests on your device? Share your experience in the comments below to help others stay vigilant.