Most of us have a ritual for the change of seasons: we open the windows, scrub the baseboards, and purge the closets of clothes that no longer fit. But as our lives migrate almost entirely into the cloud and onto glass screens, we often overlook the invisible accumulation of digital debris. The “digital junk drawer”—a collection of forgotten apps, dormant accounts, and thousands of redundant screenshots—does more than just occupy storage space; it creates a tangible drag on our hardware and a significant vulnerability in our security.
During my time as a software engineer, I saw firsthand how “bloat” isn’t just a buzzword. It is a technical reality. Every unused app that remains installed can potentially run background processes, every outdated piece of software leaves a door open for exploits, and every abandoned account is a dormant liability waiting for a data breach. Digital spring cleaning is not merely an exercise in organization; it is a critical component of modern cybersecurity and device longevity.
The necessity for this process has grown as the ecosystem of our devices has expanded. Between smartphones, tablets, laptops, and the myriad of smart-home peripherals, the average user now manages a sprawling network of identities and data points. When this network is left untended, the “attack surface”—the total sum of points where an unauthorized user can try to enter an environment—expands, leaving users exposed to risks they aren’t even aware they have.
Closing the doors on “Zombie Accounts”
The most overlooked aspect of digital hygiene is the dormant account. Many users sign up for a service, use it once, and forget it exists. These “zombie accounts” are a goldmine for cybercriminals. When a third-party service suffers a data breach, hackers often employ a technique called credential stuffing, using leaked email and password combinations to try and break into other accounts. If you have an old account on a forgotten forum from 2016 using a password you still use elsewhere, you have essentially left a key to your digital life under a very obvious mat.
Securing these accounts requires a proactive audit. The most effective method is to search your email inbox for keywords like “Welcome,” “Verify your account,” or “Subscription” to identify services you no longer use. Once identified, the goal should be total deletion rather than mere abandonment. Simply deleting the app from your phone does not delete your account or the data the company holds about you.
For those struggling to track their digital footprint, password managers can serve as a historical ledger, revealing exactly which sites have stored credentials. Updating these to unique, complex passwords—or better yet, deleting the accounts entirely—is the most impactful security move a user can make during a spring clean.
Optimizing hardware and the cost of digital bloat
Beyond security, there is the matter of performance. From an engineering perspective, a device’s efficiency is heavily dependent on how it manages its resources. Over time, applications accumulate cache files—temporary data intended to speed up loading—that can eventually become corrupted or excessively large, actually slowing the system down.
“app creep” leads to increased battery drain. Many apps request permission to refresh in the background, checking for notifications or updating location data. When dozens of unused apps do this simultaneously, the CPU never truly enters a low-power state, shortening the overall lifespan of the battery. A systematic purge of apps that haven’t been opened in 90 days can result in a noticeable increase in daily battery endurance and a snappier user interface.
The Physical Component of Digital Care
While the software side is critical, the physical state of the hardware directly impacts its performance. Dust is the enemy of electronics. In laptops and desktops, dust buildup in the cooling fans and heat sinks forces the system to work harder to maintain safe temperatures. When a device cannot cool itself, it engages in “thermal throttling,” intentionally slowing down the processor to prevent permanent heat damage.
A simple cleaning with compressed air and a microfiber cloth can prevent this. It is also worth noting that the screens and keyboards we touch thousands of times a day are breeding grounds for bacteria. Using a 70% isopropyl alcohol wipe on non-porous surfaces ensures that the device is not only running fast but is also hygienic.
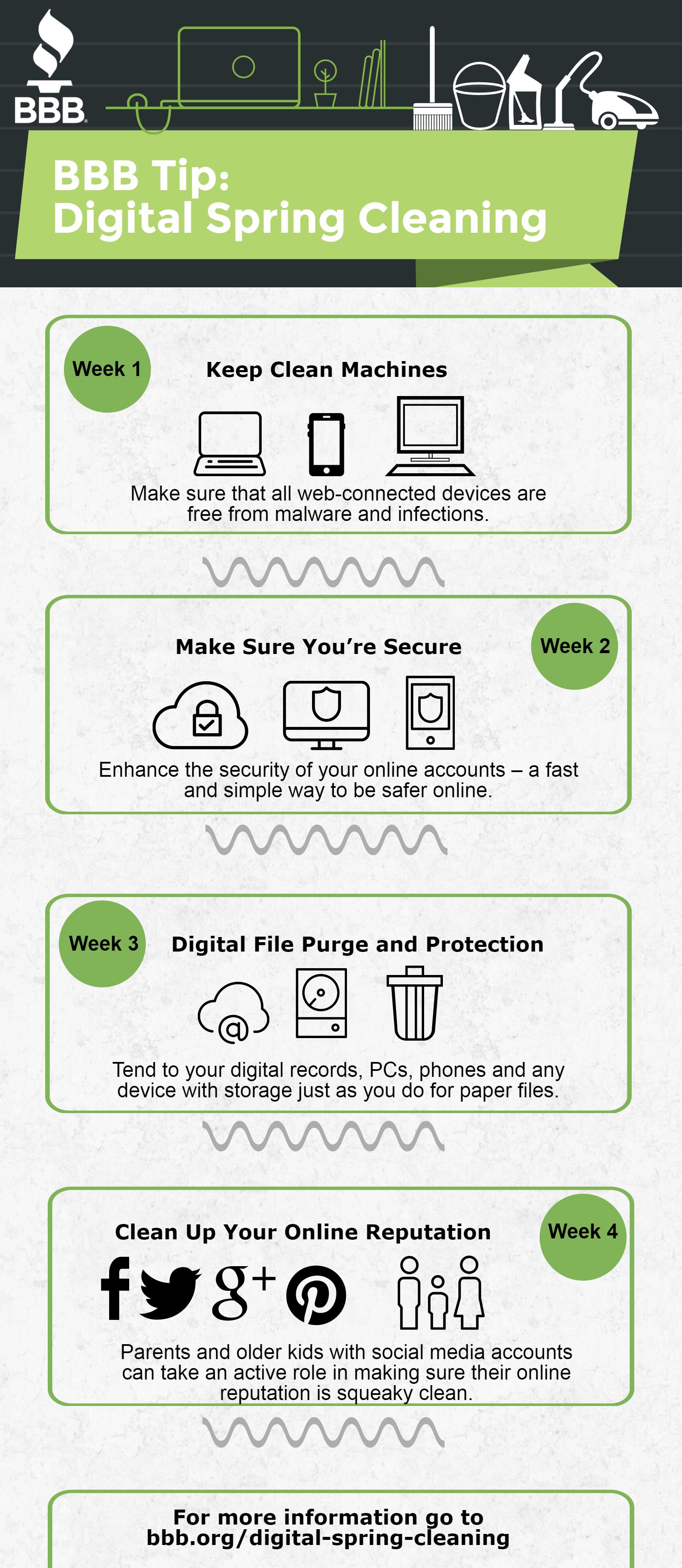
A Priority Framework for Digital Cleaning
Attempting to clean every single digital footprint in one weekend is an overwhelming task. Instead, users should approach the process based on the impact versus the effort required. Prioritizing security-critical items first ensures that the most dangerous vulnerabilities are closed before moving on to aesthetic organization.
| Task | Impact | Effort | Primary Benefit |
|---|---|---|---|
| Password Update/Audit | Critical | Medium | Cybersecurity |
| Delete Unused Accounts | High | High | Privacy/Data Protection |
| App & OS Updates | High | Low | Stability/Security |
| Clear Cache/Large Files | Medium | Low | Device Speed |
| Physical Dusting/Wiping | Medium | Low | Hardware Lifespan |
The Path to Sustainable Digital Hygiene
The goal of a digital spring cleaning should not be a one-time event, but the establishment of a sustainable habit. The tech industry is moving toward more automated solutions—such as iOS and Android’s “offload unused apps” features—but these are supplements, not replacements, for intentional management. As we move further into an era of integrated AI assistants that require even more access to our personal data, the importance of knowing exactly what data exists and where it is stored will only increase.
For those seeking official guidance on securing their accounts, the Cybersecurity & Infrastructure Security Agency (CISA) provides comprehensive resources on multi-factor authentication and password hygiene at cisa.gov.
The next major checkpoint for many users will be the upcoming wave of OS updates scheduled for the second quarter of the year, which typically introduce new privacy controls and storage management tools. Checking for these updates in the coming weeks will be the final step in ensuring your devices are lean, fast, and secure.
How do you handle your digital clutter? Do you have a system for auditing your old accounts, or is your “digital junk drawer” overflowing? Share your tips and experiences in the comments below.