The modern home is no longer just a shelter; it is a sophisticated network of sensors, microphones, and cameras designed to anticipate our every need. From the thermostat that learns our preferred temperature to the voice assistant that manages our calendars, the “smart home” promises a frictionless existence. But as these devices weave themselves into the intimate fabric of our domestic lives, the boundary between convenience and surveillance has become dangerously thin.
The allure of the Internet of Things (IoT) is built on the premise of seamless integration. However, a closer look at the architecture of these devices reveals a systemic vulnerability. Many smart gadgets are designed with a “function first, security later” mentality, leaving millions of households exposed to data leaks, unauthorized access, and an aggressive ecosystem of data brokerage that turns the private sanctuary of the home into a goldmine for advertisers.
Reporting from conflict zones and diplomatic hubs across 30 countries has taught me that the most effective surveillance is often the kind we invite inside. In those environments, bugs are hidden in walls; in the modern West, we pay a monthly subscription for the privilege of installing them ourselves. The risk is not merely a theoretical hacking scenario, but a documented reality of how consumer data is harvested and monetized.
The Architecture of Invisible Surveillance
At the heart of the smart home is the “always-on” capability. For a voice assistant to respond to a wake word, it must constantly monitor ambient sound. While manufacturers claim that recording only begins after the trigger word is detected, security researchers have repeatedly found instances of “false wakes,” where private conversations are recorded and uploaded to the cloud without the user’s knowledge.
The intrusion extends beyond audio. Modern robotic vacuums, for instance, utilize LiDAR and camera-based SLAM (Simultaneous Localization and Mapping) to navigate rooms. While this allows the device to avoid the dog’s water bowl, it also creates a high-resolution digital map of the home’s interior. This spatial data—the size of the house, the layout of the rooms, and the types of furniture owned—is incredibly valuable to marketers seeking to determine a consumer’s socioeconomic status and purchasing power.
The danger is compounded by the lack of standardized security protocols across the IoT industry. Many devices ship with hardcoded default passwords or utilize unencrypted communication channels, making them simple targets for botnets. Once a single insecure lightbulb is compromised, a sophisticated attacker can potentially move laterally through the home network to access more sensitive devices, such as laptops or security cameras.
The Data Pipeline: From Living Room to Broker
The primary product of the smart home is rarely the hardware itself; it is the data the hardware generates. This information follows a specific trajectory from the device to the corporate cloud, and often, to third-party data brokers.

| Stage | Action | Privacy Risk |
|---|---|---|
| Collection | Sensors record audio, video, or movement. | Unauthorized recording/False wakes. |
| Transmission | Data is sent to the manufacturer’s cloud. | Interception via unencrypted packets. |
| Analysis | AI parses behavior and preferences. | Creation of invasive psychological profiles. |
| Monetization | Insights are sold to advertisers/brokers. | Loss of anonymity and targeted manipulation. |
This pipeline creates a “digital twin” of the user. By analyzing when you wake up, what you ask your assistant, and how often you move from room to room, companies can infer health issues, relationship stresses, or pregnancy long before the user has shared that information explicitly. This isn’t just about seeing an ad for a product you mentioned; it is about the systemic erosion of the “expectation of privacy” within the home.
Stakeholders and the Struggle for Regulation
The tension over smart home privacy pits three primary groups against one another: the tech giants, the consumers, and the regulators.
- Tech Giants: Companies like Amazon, Google, and Samsung argue that data collection is essential for improving AI and providing the “magic” of a personalized home. They emphasize user consent, though that consent is often buried in tens of thousands of words of legal jargon.
- Consumers: Most users operate on a “convenience trade-off,” accepting the risks because the utility of the device outweighs the abstract fear of data harvesting. However, a growing segment of “privacy-first” consumers is pushing for local-only processing.
- Regulators: In the European Union, the GDPR (General Data Protection Regulation) has forced more transparency. In the U.S., the landscape is a patchwork of state laws like the CCPA in California, leaving many consumers without a federal baseline of protection.
“The problem is that we are treating the home as an extension of the internet, rather than treating the internet as a tool for the home. When the network becomes the master, the home is no longer a private space.”
Securing the Domestic Perimeter
While completely disconnecting from the IoT ecosystem is impractical for many, cybersecurity experts recommend a “defense-in-depth” strategy to mitigate the most egregious risks. The goal is to limit the amount of data leaving the house and to ensure that if one device is breached, the rest of the network remains secure.
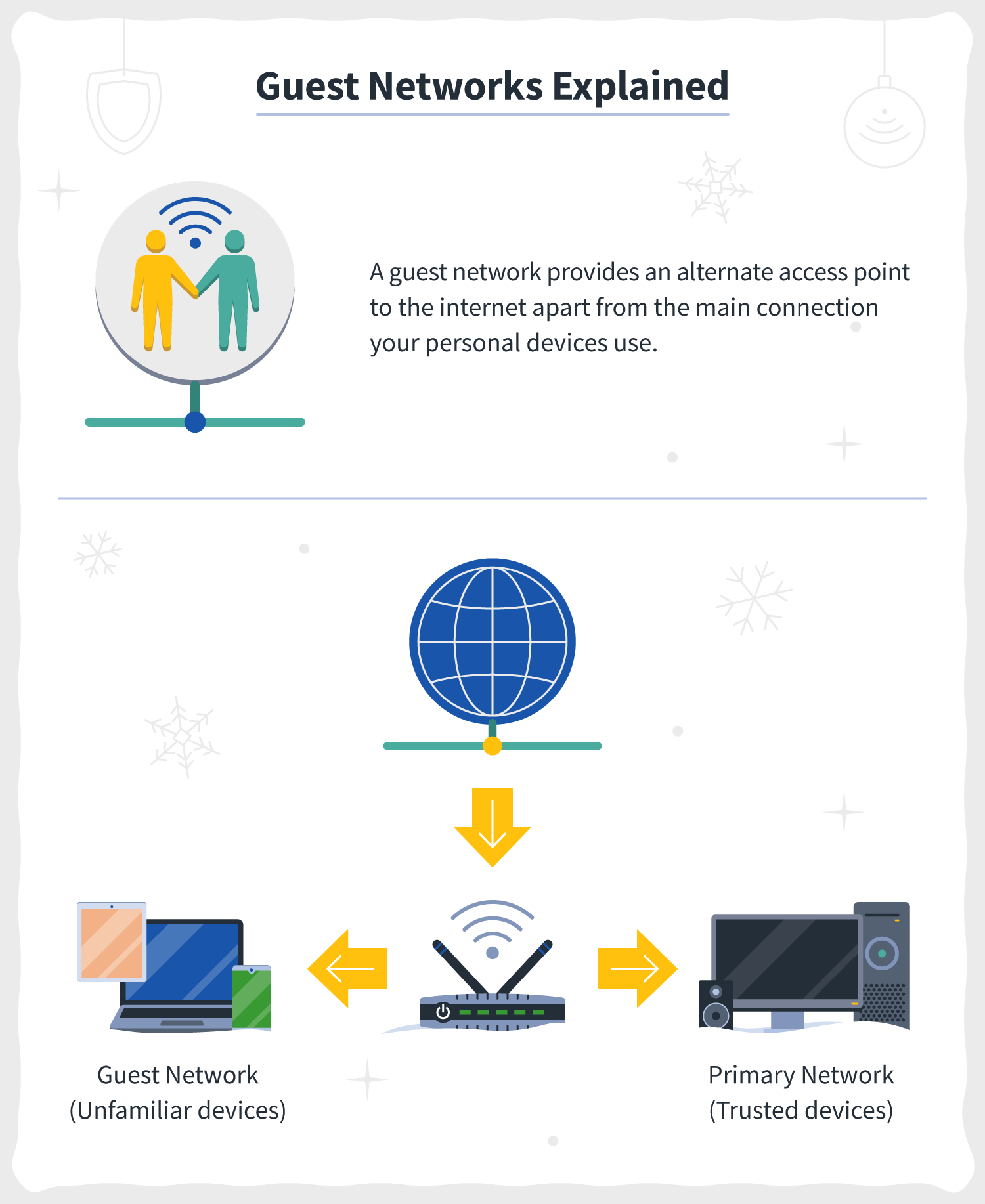
One of the most effective methods is network segmentation. By setting up a “Guest Network” specifically for smart devices, users can isolate their lightbulbs and smart plugs from the primary network where they store banking information and private documents. If a smart plug is hacked, the attacker is trapped in a digital cul-de-sac, unable to reach the family computer.
users should audit their “permissions” regularly. Many apps associated with smart devices request access to the phone’s contacts, location, and microphone even when those functions are not necessary for the device to operate. Disabling these unnecessary permissions reduces the footprint of data being harvested.
Note: This article is provided for informational purposes only and does not constitute professional cybersecurity or legal advice. For specific security audits, consult a certified information systems security professional (CISSP).
The next major checkpoint for smart home privacy will be the widespread adoption of the Matter standard, a unifying protocol backed by Apple, Google, and Amazon. While Matter aims to make devices from different brands work together, the industry is watching closely to see if it will also implement standardized, mandatory security and privacy benchmarks, or if it will simply streamline the way data is collected across platforms.
Do you prioritize convenience or privacy in your home? Share your thoughts and your best security tips in the comments below.

