For many DevOps engineers, the choice of an operating system is often dictated not by technical preference, but by the limitations of their cloud provider. Many platforms offer a restrictive menu of pre-configured virtual machines, blocking the ability to upload custom images or boot from an ISO. This “walled garden” approach creates a significant hurdle for those looking to deploy specialized, high-security environments like Talos Linux.
Talos Linux represents a fundamental shift in how we think about the node operating system. Unlike traditional distributions, This proves an immutable, API-managed OS designed exclusively for Kubernetes. It strips away almost everything a human administrator typically uses—there is no shell, no SSH access, and no traditional package manager. By removing these executables, Talos drastically reduces the attack surface, turning the node into a secure appliance that handles the full lifecycle of Kubernetes control-plane components.
While Sidero Labs provides pre-built images for major providers, the restrictive nature of certain environments often makes a standard rollout impossible. However, there is a reliable way to install Talos Linux on any machine, regardless of the provider’s restrictions, by leveraging a deep-seated Linux kernel mechanism called kexec.
The process essentially turns an existing, provider-approved Linux installation into a temporary bootloader. By using kexec, engineers can hot-swap the running kernel for the Talos kernel without requiring a physical reboot or access to the BIOS/UEFI. This allows the system to transition from a general-purpose OS, such as Ubuntu, directly into a Talos environment running entirely in RAM.
The Security Logic of an OS Without a Shell
To understand why engineers go to such lengths to install Talos, one must understand the philosophy of “minimalism as security.” In a standard Linux environment, the presence of a shell and SSH provides a convenient entry point for administrators, but it also provides a foothold for attackers. Once a perimeter is breached, these tools are often used for lateral movement and privilege escalation.
Talos eliminates this risk by removing the shell entirely. All configuration is handled through a Kubernetes-like API. If a change is needed, it is pushed via a machine-config file rather than executed via a command line. This ensures that the state of the machine is always known, reproducible, and audited, moving the industry closer to a truly “infrastructure as code” reality.
Bypassing Restrictions with kexec
The primary obstacle in restrictive environments is the inability to change the boot image. The kexec utility solves this by allowing a system to boot into a new kernel from the currently running one. It is a system call that tells the current kernel to load a new kernel image and initramfs into memory and then jump directly to it.
To begin this process on a machine running a standard distribution like Ubuntu, the first step is installing the necessary tools. A simple apt install kexec-tools -y command prepares the environment. From there, the Talos kernel (vmlinuz) and initramfs must be downloaded from the official Sidero Labs repository.
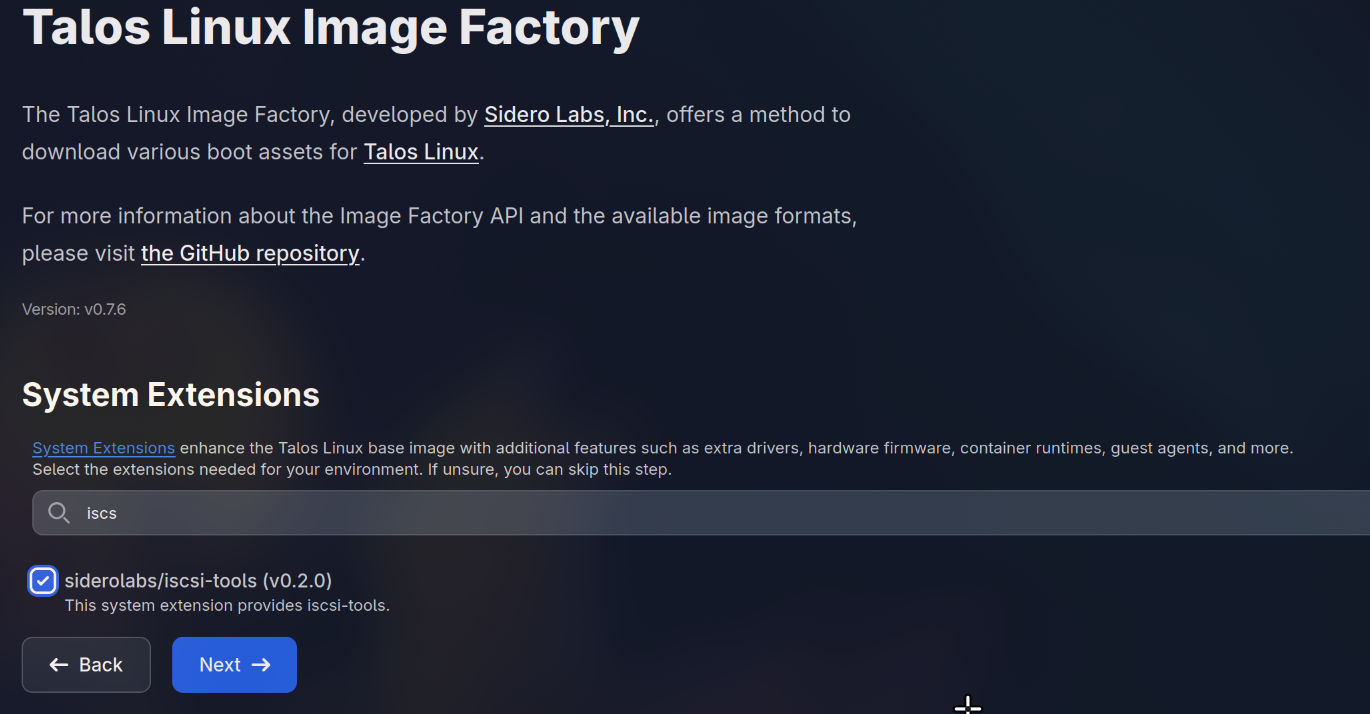
For those deploying on physical bare-metal hardware where specific firmware is required, the Talos Factory service can be used to build a custom image. Alternatively, the Cozystack project—a cloud-building solution currently in the CNCF Sandbox—provides pre-built images that include a wider array of necessary modules and firmware for diverse hardware profiles.
The most critical part of the kexec transition is the kernel command line. Because Talos is booting into RAM, it needs to know how to talk to the network immediately. By using the ip= parameter—a built-in feature of the Linux kernel enabled by CONFIG_IP_PNP—administrators can pass the IP address, gateway, and netmask directly to the kernel at boot time. This ensures that as soon as the system switches to Talos, it is reachable via the API.
From RAM to Persistent Disk
Once the kexec command is executed, the machine is running Talos Linux, but it is volatile. A reboot would return the system to the original provider-installed OS. To make the installation persistent, the administrator must apply a machine-config that instructs Talos to install itself onto the physical disk, overwriting the previous operating system.
This is typically handled via talosctl, the official command-line tool for managing Talos clusters. The process involves generating a secret, creating a configuration patch that specifies the target disk (e.g., /dev/sda) and network settings, and applying that config to the node. Once the talosctl apply command is issued, the node writes the bootloader to the disk and reboots into a permanent Talos state.
For those managing larger fleets of nodes, manual configuration becomes a bottleneck. This is where Talm, a configuration manager developed by the Cozystack team, becomes valuable. Talm functions similarly to Helm for Kubernetes. it uses templates and lookup functions to dynamically query the Talos API and substitute values into the final config.
The advantage of Talm is twofold: it simplifies the management of node-specific differences (like varying disk names or network interfaces) and it separates secrets from the configuration. Because the generated configs do not contain sensitive data, they can be safely stored in Git repositories, while secrets are kept in dedicated files like secrets.yaml.
Comparing Configuration Workflows
Choosing between the official talosctl and the community-driven Talm depends largely on the scale of the deployment. While talosctl is the gold standard for single-node tests or slight clusters, Talm is designed for the complexities of bare-metal clouds.

| Feature | talosctl (Official) | Talm (Cozystack) |
|---|---|---|
| Config Method | Static YAML / Patches | Helm-like Templates |
| Secret Handling | Embedded in Config | Separated/External |
| Node Discovery | Manual Specification | Dynamic API Lookup |
| Git Compatibility | Requires Encryption | Native (Secret-less) |
The Path to Immutable Infrastructure
The ability to deploy Talos Linux on any provider removes the final barrier to adopting a truly immutable infrastructure. By treating the operating system as a versioned artifact rather than a living entity that requires patching and SSH maintenance, organizations can significantly increase their security posture and reduce operational drift.
As the ecosystem evolves, the integration between API-driven operating systems and cloud-native orchestration will likely deepen. The next major milestone for users of this method will be the continued refinement of the Sidero Labs toolchain, specifically regarding automated bare-metal provisioning and the expansion of the Cozystack project within the CNCF ecosystem.
We want to hear from the community: have you attempted to bypass cloud provider restrictions using kexec, or are you sticking with managed OS options? Share your experiences in the comments below.

