For most iPhone users, a locked screen is the primary line of defense against data theft. Whether This proves a complex alphanumeric passcode or a biometric scan, the assumption is that once the device is locked, the contents—and the financial accounts linked to them—are secure. Although, a specific vulnerability in how some devices handle “locked” states allows sophisticated thieves to bypass these barriers and potentially drain funds from a locked iPhone.
This exploit does not rely on guessing a passcode or utilizing a software bug in the operating system itself. Instead, it leverages a gap in the “Lock Screen” settings that allows certain high-value functions to remain accessible even when the phone is not unlocked. By accessing these specific portals, bad actors can initiate password resets for critical accounts or execute transactions through integrated digital wallets.
The primary goal for these thieves is often not the hardware itself, but the “digital keys” stored within. By gaining access to a user’s phone number via the lock screen, they can trigger “forgot password” requests for banking apps, email accounts, and cryptocurrency wallets, effectively locking the legitimate owner out of their own financial life while the thief transfers funds.
The Mechanics of the Lock Screen Exploit
The vulnerability centers on the USB Accessories and Control Center settings. By default, some iPhones allow accessories to connect to the device even when it is locked. While this is convenient for charging or syncing, it can be exploited by specialized hardware designed to brute-force or bypass certain security layers.
More critically, if the “Control Center” is accessible from the lock screen, a thief can toggle Airplane Mode, Wi-Fi, and Cellular data. This allows them to manipulate the device’s connectivity to intercept SMS-based two-factor authentication (2FA) codes. Because many financial institutions still rely on SMS as a primary recovery method, a thief who can see a notification on a locked screen—or manipulate the connection to receive a code—can reset a password in minutes.
Once the thief has reset the password for a primary email account (like Gmail or iCloud), they have a master key. From there, they can navigate to “Forgot Password” links for banking apps, redirect the recovery emails to their own devices, and authorize high-value transactions. This process is often faster than the victim’s realization that the phone is missing.
Who is Most at Risk?
While any iOS user could be targeted, those who rely heavily on SMS for security are the most vulnerable. The risk increases for users who have not enabled “Stolen Device Protection,” a feature introduced by Apple to mitigate these exact scenarios. Those with high-value assets in fintech apps or cryptocurrency exchanges are primary targets for this specific method of theft.
| Feature | Default State | Risk Factor |
|---|---|---|
| Control Center | Enabled | Allows toggling of network settings to intercept codes. |
| USB Accessories | Enabled | Allows external hardware to communicate with the device. |
| Lock Screen Notifications | Visible | Reveals 2FA codes via “preview” text. |
| Siri | Enabled | Can sometimes be used to query personal info. |
How to Protect Your Funds and Data
The most effective way to prevent thieves from draining funds from a locked iPhone is to harden the lock screen settings. This removes the “entry points” that allow a thief to interact with the device’s connectivity or hardware without the passcode.
To secure your device, navigate to Settings > Face ID & Passcode (or Touch ID). Under the “Allow Access When Locked” section, you should disable the following options:
- Control Center: Turning this off prevents thieves from toggling Airplane Mode or Wi-Fi.
- USB Accessories: Disabling this ensures that no one can plug in a device to attempt to bypass the lock screen.
- Siri: Prevents unauthorized voice queries that might reveal personal data.
- Notification Previews: Set these to “When Unlocked” so that 2FA codes sent via SMS do not appear on the screen for anyone to see.
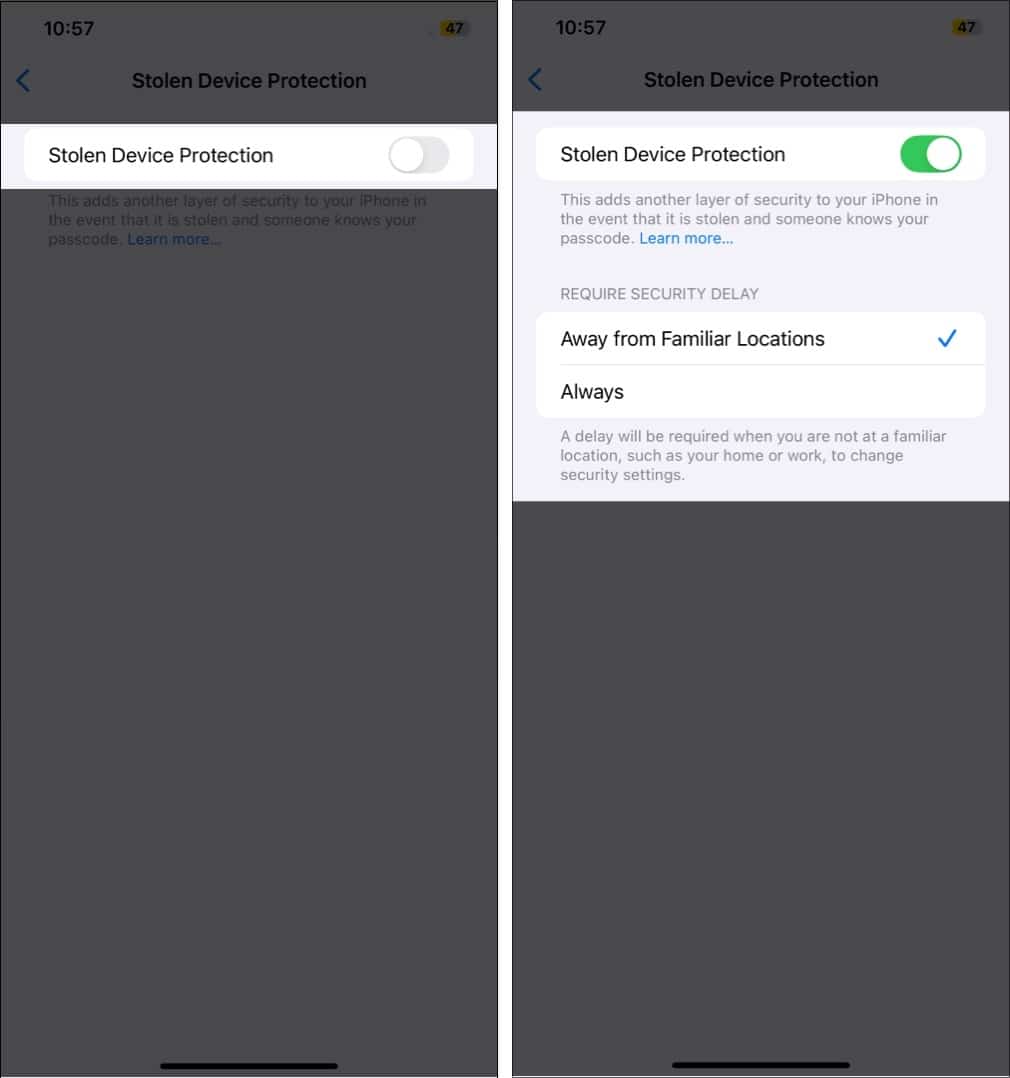
users should enable Stolen Device Protection. This feature adds a layer of security by requiring a biometric scan (Face ID or Touch ID) for critical actions—such as changing the Apple ID password—and imposes a one-hour security delay if the device is in an unfamiliar location. This delay prevents a thief from immediately changing your credentials even if they somehow obtain your passcode.
Moving Beyond SMS Authentication
From a financial security perspective, the most critical step is moving away from SMS-based two-factor authentication. Because SMS is tied to the SIM card and the device, it is a single point of failure. Security experts recommend using authenticator apps (like Google Authenticator or Authy) or physical security keys (like YubiKey).
Authenticator apps generate codes locally on the device and do not rely on the cellular network, making them significantly harder to intercept via lock-screen exploits. For those managing high-value accounts, switching to a hardware-based key is the gold standard in preventing unauthorized access.
The Broader Impact of Digital Theft
This trend reflects a shift in criminal tactics. Physical theft of hardware is now secondary to “identity theft via hardware.” When a thief steals a phone, they aren’t just stealing a piece of glass and aluminum; they are stealing a gateway to the victim’s entire financial ecosystem. The speed at which these attacks occur—often within minutes of the theft—leaves users with very little time to react via “Locate My” or remote wipe functions.

The psychological impact is often greater than the financial loss. The feeling of a “locked” device being breached creates a sense of total vulnerability. This is why the move toward biometric-only changes for sensitive settings is a critical evolution in mobile security.
Disclaimer: This article is for informational purposes only and does not constitute legal or professional financial advice.
Apple continues to update its security protocols with each iOS release. The next major checkpoint for users will be the rollout of further refinements to Stolen Device Protection and potential changes to how eSIMs are handled to prevent “SIM swapping” during physical thefts. Users are encouraged to keep their software updated to the latest version of iOS to ensure they have the latest security patches.
Do you have a security tip for protecting your mobile devices? Share your thoughts in the comments below.

