A single threat actor is responsible for the vast majority – 83% – of recent exploitation attempts targeting critical vulnerabilities in Ivanti Endpoint Manager Mobile (EPMM), according to new threat intelligence. The attacks, focusing on vulnerabilities CVE-2026-21962 and CVE-2026-24061, have been actively exploited in what security researchers are calling zero-day attacks, prompting Ivanti to release emergency hotfixes.
The vulnerabilities allow attackers to inject code without authentication, potentially granting them remote code execution (RCE) on vulnerable systems. This means an attacker could take control of affected devices without needing a username or password. The scale of the attacks, and the concentration of activity around a single source, is raising concerns among cybersecurity professionals.
Single Actor Dominates Exploitation Efforts
Threat intelligence firm GreyNoise identified the primary source of the attacks as a single IP address – 193[.]24[.]123[.]42 – hosted by PROSPERO OOO (AS200593). Censys analysts have labeled PROSPERO OOO as a “bulletproof autonomous system,” meaning it’s infrastructure known to host malicious activity and resist takedown efforts. Between February 1st and 9th, GreyNoise observed 417 exploitation sessions originating from eight unique IP addresses, with the single IP address accounting for a staggering 83% of all activity.
Source: GreyNoise
The activity peaked sharply on February 8th, with 269 recorded sessions – nearly thirteen times the daily average of 22. This concentrated burst of exploitation underscores the urgency of addressing the vulnerabilities.
Initial Access Broker Activity Suspected
Researchers likewise noted that 85% of the exploitation sessions (354 out of 417) utilized OAST-style DNS callbacks. This technique is commonly used to verify command execution capability, suggesting the attacks are linked to initial access brokers – entities that gain access to systems and then sell that access to other malicious actors. This indicates the attackers may not be directly targeting Ivanti EPMM systems for their own purposes, but rather establishing a foothold for future, potentially more damaging, attacks.
Interestingly, initial reports of indicators of compromise (IoCs) pointed to IP addresses associated with Windscribe VPN (185[.]212[.]171[.]0/24). However, GreyNoise telemetry revealed these IPs were primarily scanning for Oracle WebLogic instances, not actively exploiting the Ivanti vulnerabilities. This highlights the importance of relying on accurate and verified threat intelligence, as chasing false leads can divert valuable security resources.
Broader Targeting Beyond Ivanti
The threat actor behind these attacks isn’t solely focused on Ivanti EPMM. GreyNoise’s research indicates the same IP address (193[.]24[.]123[.]42) has also been exploiting vulnerabilities in Oracle WebLogic (CVE-2026-21962), GNU Inetutils Telnetd (CVE-2026-24061), and GLPI (CVE-2025-24799). The Oracle WebLogic flaw saw the most activity, with 2,902 sessions, followed by Telnetd with 497 sessions. This broader targeting suggests a sophisticated and opportunistic attacker leveraging automated tools to exploit multiple vulnerabilities simultaneously.
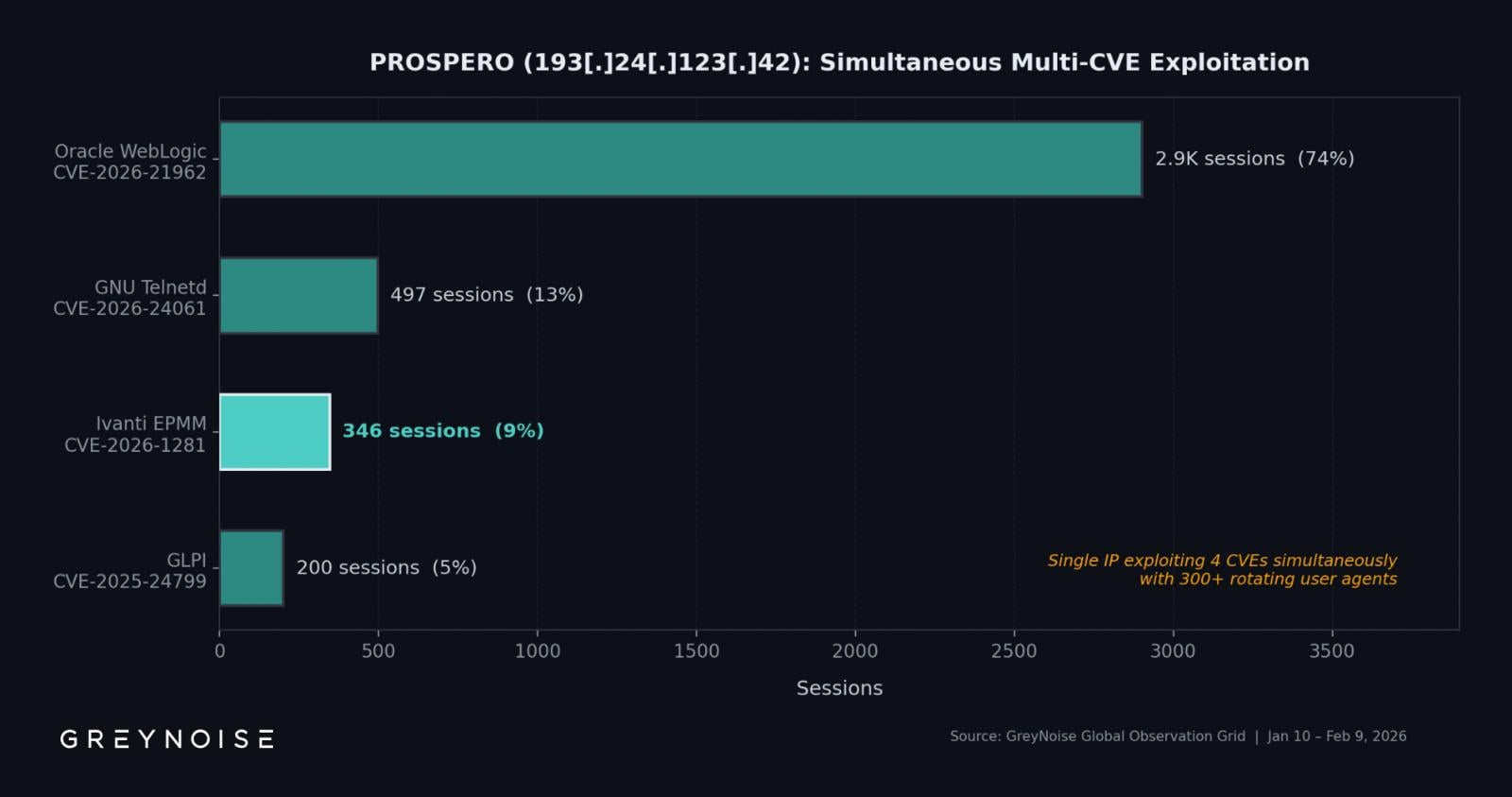
Source: GreyNoise
The exploitation activity appears to be fully automated, rotating through approximately 300 different user agents, further indicating a large-scale, systematic campaign.
Mitigation and Ongoing Concerns
Ivanti has released hotfixes for the vulnerabilities, but acknowledges that these are not permanent solutions. The company has promised a complete patch with the release of EPMM version 12.8.0.0, expected in the first quarter of 2026. In the interim, Ivanti recommends using specific RPM packages for affected EPMM versions (12.5.0.x, 12.6.0.x, 12.7.0.x, 12.5.1.0, and 12.6.1.0). The most conservative approach, according to Ivanti, is to rebuild the EPMM instance and migrate all data to the new system, with detailed instructions available on their forums.
The concentration of exploitation activity around a single, bulletproof-hosted IP address underscores the challenges organizations face in defending against sophisticated attackers. Relying solely on publicly available indicators of compromise may prove insufficient, as demonstrated by the misdirection surrounding the Windscribe VPN IPs. Organizations should prioritize proactive threat hunting and leverage comprehensive threat intelligence feeds to identify and mitigate these risks.
Ivanti is expected to release the full patch for EPMM version 12.8.0.0 within the first quarter of 2026. Security teams should continue to monitor for updates and implement the recommended mitigations in the meantime.
Have thoughts on this developing story? Share your comments below and let us know how these vulnerabilities are impacting your organization.
