For most CTOs and privacy officers, the goal has always been simple: keep the data safe and avoid the nightmare of a public breach. But in California, the standard is shifting from “doing your best” to “proving it to a third party.” The California Privacy Protection Agency (CPPA) is moving beyond general guidelines, introducing mandatory, independent cybersecurity audits that will force qualifying businesses to open their books—and their server logs—to outside scrutiny.
This isn’t just another checkbox for the compliance department. For the first time, the state is requiring a certified, independent auditor to verify that a company’s security claims match its actual practices. If you’re a business processing large volumes of consumer data or making a living by selling it, the clock is already ticking. The rollout is staggered, but the requirements are rigid, and the personal stakes for executives are higher than they’ve ever been.
Coming from a software engineering background, I’ve seen how “compliance” often becomes a paper exercise—a set of policies that look great in a PDF but aren’t reflected in the actual codebase or network architecture. The CPPA is clearly trying to kill that culture. By requiring independent audits and executive certifications under penalty of perjury, California is treating cybersecurity less like a best practice and more like a financial audit.
Who Falls Under the ‘Significant Risk’ Umbrella?
Not every business operating in California will be subject to these audits. The CPPA has narrowed the scope to businesses whose data processing presents a “significant risk to consumers’ security,” as defined under 11 CCR § 7120. In plain English, the state is targeting the companies that have the most to lose—and the most power to cause harm if they are breached.
A business is flagged as a “significant risk” if it meets either of two primary thresholds. First, any company that derives 50 percent or more of its annual revenue from selling or sharing personal information is automatically in scope, regardless of how many people’s data they handle. This essentially captures the data-broker economy.
Second, the rules apply to larger enterprises that hit a revenue ceiling of $25 million and meet one of two data-volume benchmarks: processing the personal information of 250,000 or more consumers or households, or processing the sensitive personal information—think Social Security numbers, precise geolocation, or health data—of 50,000 or more consumers.
The Implementation Timeline: A Staggered Rollout
The CPPA isn’t requiring everyone to comply tomorrow. Instead, they’ve created a tiered deadline system based on annual revenue. The larger the company, the sooner the deadline hits, reflecting the agency’s belief that bigger firms have the resources to move faster.

| Revenue Bracket | First Audit Due Date | Audit Coverage Period |
|---|---|---|
| Exceeding $100 Million | April 1, 2028 | Jan 1, 2027 – Jan 1, 2028 |
| $50 Million – $100 Million | April 1, 2029 | Jan 1, 2028 – Jan 1, 2029 |
| Under $50 Million | April 1, 2030 | Jan 1, 2029 – Jan 1, 2030 |
Once the initial window closes in 2030, these audits become a permanent annual fixture. Every qualifying business must submit its report to the CPPA by April 1 of each year. For companies hitting the $100 million mark now, the “preparation phase” is effectively already underway; they need to ensure their 2027 activities are documented and secure to pass the 2028 audit.
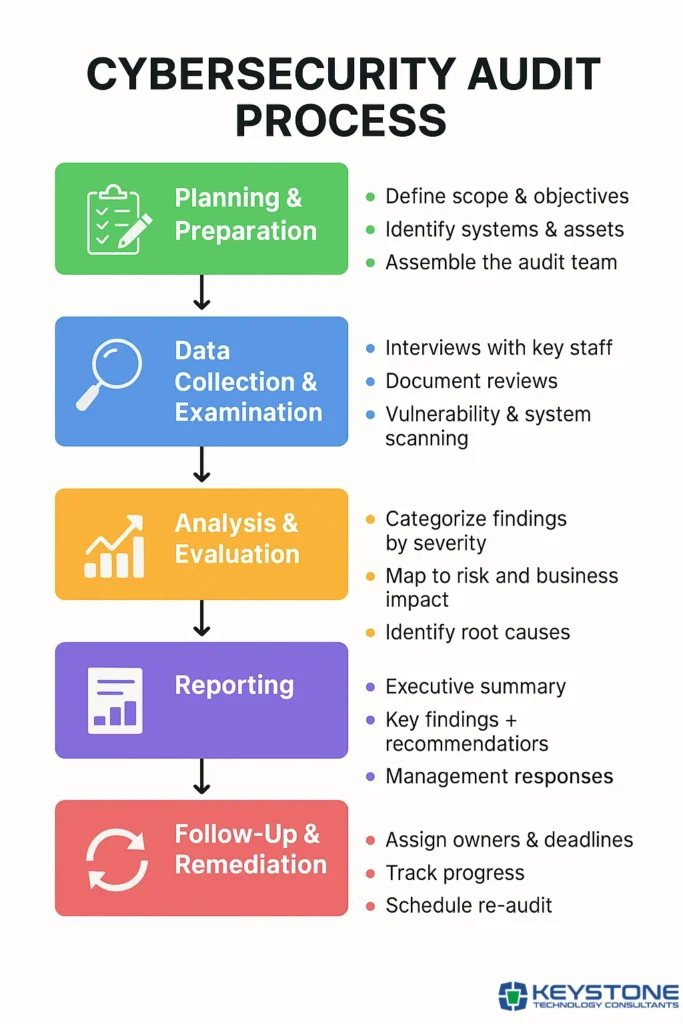
What the Auditors Are Actually Looking For
This is where the technical rubber meets the road. The CPPA isn’t asking for a high-level summary; they are requiring an assessment of the entire cybersecurity program. An independent auditor will dig into the actual implementation of security controls, meaning “we have a policy for this” will no longer be a sufficient answer.
Key areas of focus include:
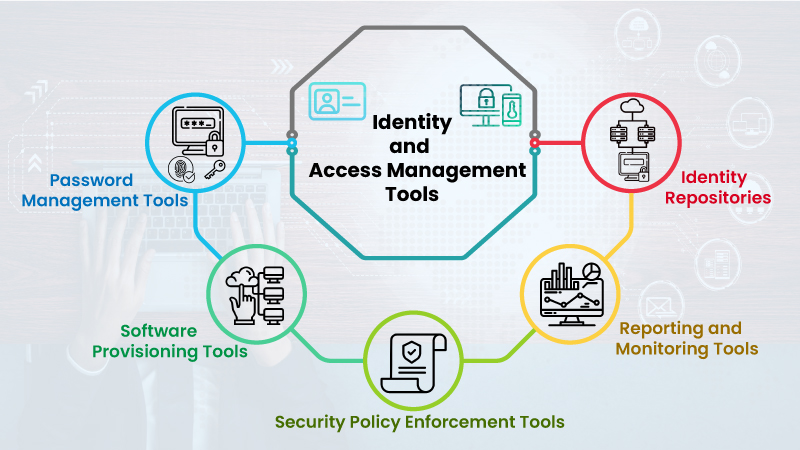
- Identity and Access Management: Rigorous checks on multifactor authentication (MFA) and strict access controls to ensure the principle of least privilege is enforced.
- Data Protection: Verification of encryption standards for data both at rest and in transit.
- Network Resilience: Evaluation of network monitoring tools and the effectiveness of incident response planning.
- The Human Element: Review of employee training programs and the actual practices used for secure data disposal.
Crucially, the auditor must remain fully independent. The final report cannot rely on the management team’s own assertions. If the auditor finds a gap—such as a legacy database that isn’t encrypted or a failure to offboard former employees—the report must document the flaw and include a concrete plan from the company to fix it.
Executive Accountability and the ‘Perjury’ Clause
Perhaps the most striking part of the new regulations is the submission process. The audit isn’t just a report filed in a folder; it requires a written certification from an executive with direct responsibility for cybersecurity compliance.
This executive must sign the certification under penalty of perjury. This moves the risk from a corporate fine to a potential personal legal liability. By requiring a signature under penalty of perjury, the CPPA is signaling that “willful ignorance” regarding security gaps will not be an acceptable defense. It forces a direct line of communication between the technical teams on the ground and the C-suite.
Disclaimer: This article is provided for informational purposes only and does not constitute legal advice. Businesses should consult with qualified legal counsel to determine their specific compliance obligations under the CCPA and CPPA regulations.
As the CPPA continues to refine its regulatory framework, the next major checkpoint will be the agency’s ongoing rulemaking sessions and potential updates to the 11 CCR guidelines, which may further clarify the “significant risk” definitions. Companies are encouraged to monitor official updates directly via the California Privacy Protection Agency website.
Do you think independent audits will actually make consumer data safer, or is this just more regulatory red tape for tech companies? Let us know in the comments.

