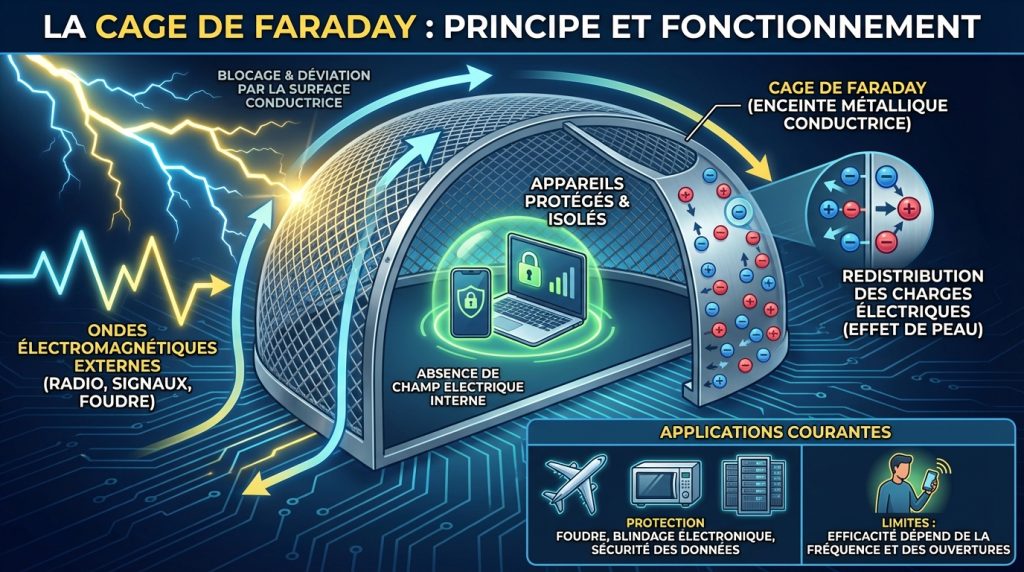
For decades, the “air gap” has been the gold standard of cybersecurity. By physically disconnecting a computer from all networks—no Wi-Fi, no Ethernet, no Bluetooth—organizations believed they had created an impenetrable fortress. For the most sensitive secrets, like nuclear launch codes or high-level intelligence, a Faraday cage is often added to the mix, a grounded metal enclosure designed to block all external electromagnetic interference and prevent any signals from leaking out.
But a new class of malware known as ODINI has effectively turned that fortress into a sieve. By exploiting the fundamental laws of physics, ODINI can exfiltrate data from these isolated systems by modulating the magnetic emissions produced by the CPU itself. Because these low-frequency magnetic fields can pass through the conductive materials that stop radio waves, the traditional Faraday cage—once thought to be the ultimate shield—is rendered largely irrelevant.
As a former software engineer, I’ve seen many “unhackable” systems fall to clever exploits, but ODINI is particularly unsettling because it doesn’t rely on a software bug or a misplaced password. It relies on the fact that electricity creates magnetism. Every time a CPU processes data, it consumes power, and that power consumption creates a magnetic field. ODINI simply learns how to “play” that field like an instrument, broadcasting binary data to a nearby receiver.
The physics of a magnetic leak
Most air-gap breaches rely on radio frequency (RF) emissions. Researchers have previously shown that malware can turn a computer’s memory bus or GPU into a makeshift radio transmitter. However, RF signals are easily blocked by a Faraday cage, which redistributes the electrical charge around the exterior of the enclosure, keeping the interior isolated.
ODINI takes a different path. Instead of generating high-frequency radio waves, it manipulates the CPU’s power consumption to create low-frequency magnetic fluctuations. By rapidly switching the CPU between high-load and low-load states, the malware creates a magnetic “pulse” that corresponds to 1s and 0s. These magnetic fields are not stopped by the thin aluminum or copper sheets used in standard Faraday shielding; they require specialized, high-permeability materials like Mu-metal to be contained.
The receiver for this attack is surprisingly mundane: a standard smartphone. Most modern phones are equipped with a magnetometer—the sensor used for the digital compass. ODINI-infected systems can transmit data to a phone placed within a few centimeters or meters of the chassis, allowing an attacker to “listen” to the CPU’s magnetic heartbeat and reconstruct the stolen data.
The attack sequence: From CPU to Smartphone
The breach occurs in a precise sequence of events that bypasses almost every traditional digital security layer:
- Infection: The target system is infected via a “bridge” (such as a compromised USB drive or a malicious insider).
- Data Selection: The malware identifies high-value targets, such as RSA encryption keys or administrative passwords.
- Magnetic Modulation: ODINI modulates the CPU’s workload, creating specific magnetic patterns that represent the binary data of the stolen files.
- External Capture: An attacker places a smartphone near the computer. The phone’s magnetometer picks up the fluctuations.
- Decoding: A custom app on the phone converts the magnetic pulses back into readable text or files.
Why this changes the risk calculus
The primary concern for security professionals is not the speed of the attack—which is relatively slow compared to a network transfer—but the stealth and the target. ODINI isn’t designed to steal terabytes of data; it is designed to steal the “crown jewels”: small strings of text, such as cryptographic keys, that can unlock vast amounts of other data.
This vulnerability creates a critical gap for stakeholders in national defense, aerospace, and high-finance sectors. These organizations have invested millions in physical shielding, believing that if a machine is not connected to the internet and is encased in metal, it is safe. ODINI proves that physical isolation is a deterrent, not a guarantee.
| Method | Transmission Medium | Blocked by Faraday Cage? | Primary Receiver |
|---|---|---|---|
| RF-Based | Radio Waves | Yes | SDR (Software Defined Radio) |
| Acoustic | Ultrasonic Sound | No | Microphone |
| ODINI | Magnetic Fields | No | Magnetometer (Smartphone) |
The limits of the breach
Despite its sophistication, ODINI is not a “magic bullet” for hackers. It has significant operational constraints that prevent it from being a widespread threat to the average consumer. First, the physical proximity required is steep; the attacker must be close enough for the magnetometer to detect the signal, which usually means being in the same room as the target hardware.
Second, the data transfer rate is incredibly low. While a network connection can move gigabits per second, magnetic exfiltration moves bits per second. This makes it useless for stealing large databases but perfectly suited for stealing a 256-bit AES key.
Finally, the “noise” of a modern office—other electronics, power cables, and metal furniture—can interfere with the signal. The attack requires a relatively clean magnetic environment or a very high-gain sensor to be effective.
Closing the magnetic loophole
Stopping ODINI requires a shift from digital security to physical engineering. Standard Faraday cages are no longer sufficient for the highest levels of security. Engineers are now looking toward “magnetic shielding,” which involves using materials with high magnetic permeability to divert the magnetic flux around the sensitive equipment.
On the software side, some researchers suggest implementing “noise-generating” processes. By running randomized CPU workloads in the background, a system could effectively “jam” its own magnetic emissions, making it impossible for an external sensor to distinguish between actual data and random noise.
As the security community digests these findings, the focus will likely shift toward certifying hardware based on its magnetic footprint. The next major checkpoint for this research will be the presentation of updated mitigation frameworks at upcoming cybersecurity summits, where experts will determine if standardized “magnetic masking” can be integrated into enterprise-grade hardware.
Do you think physical air-gapping is still viable in the age of side-channel attacks? Let us know your thoughts in the comments or share this story with your IT security team.

