Sweden has identified a pro-Russian group with ties to Moscow’s security and intelligence services as the perpetrator of a cyberattack on a heating plant last year. The revelation, made public on Wednesday, marks the first time Swedish authorities have officially detailed the incident, which targeted critical energy infrastructure in the western part of the country.
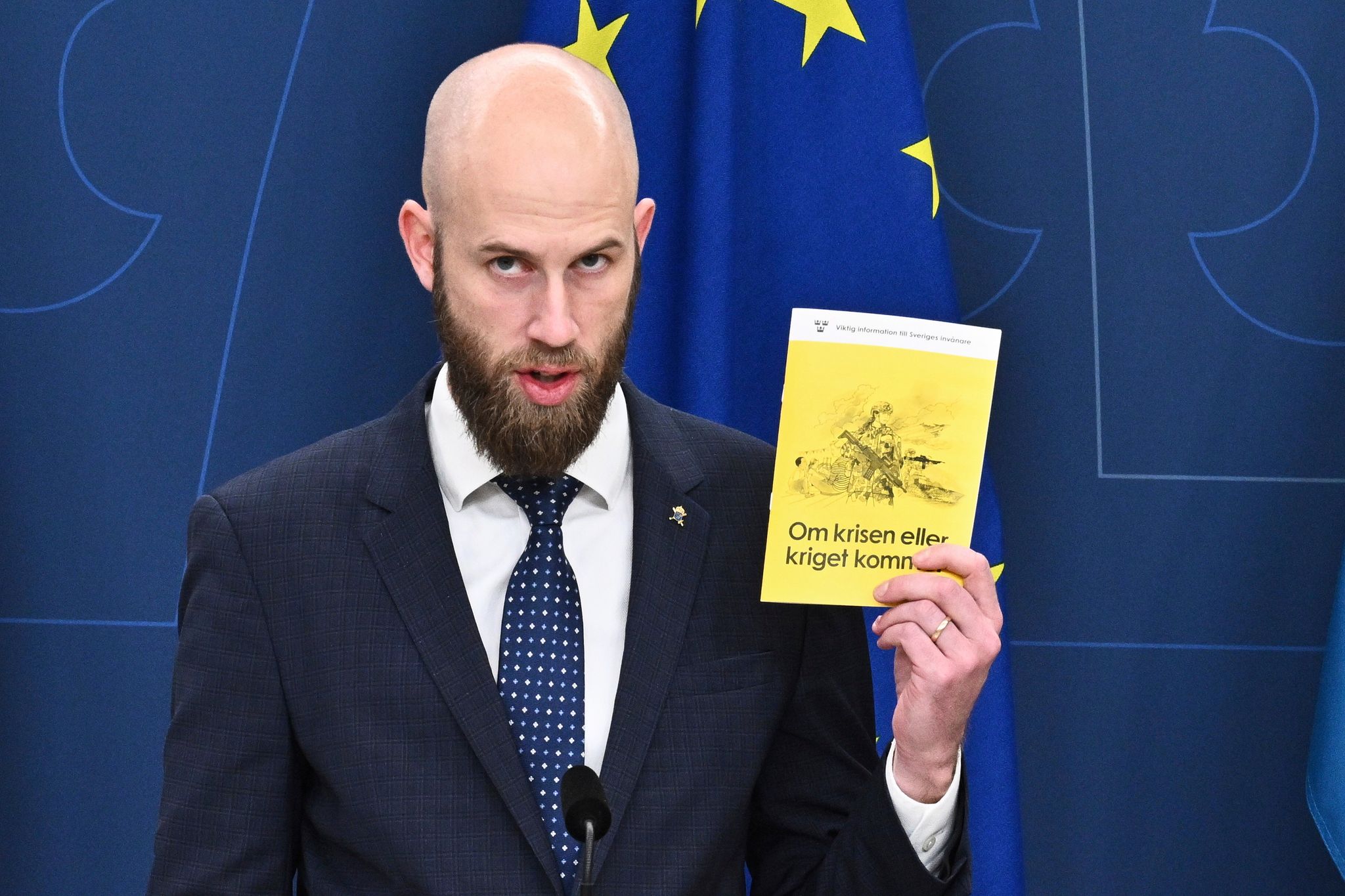
Although the attempt ultimately failed, the Swedish government is framing the incident as part of a broader, coordinated campaign of hybrid warfare. Carl-Oskar Bohlin, Sweden’s minister for civil defense, characterized the operation as an example of “risky and careless behavior” by Russia, noting that such attacks target the very systems that maintain societal stability.
The announcement comes amid a surge of warnings from neighboring Nordic and Baltic states. Officials in Poland, Norway, Denmark, and Latvia have all recently reported similar incursions into their critical infrastructure, suggesting a systemic effort by Russian-linked actors to probe vulnerabilities across Europe’s energy and utility grids.
This specific Sweden blames pro-Russian group for cyberattack last year on its energy infrastructure case is not an isolated event but rather a piece of a larger puzzle. Since the full-scale invasion of Ukraine in February 2022, Western officials have tracked more than 150 incidents of sabotage and malign activity across the continent, ranging from digital intrusions to physical arson.
A Pattern of Infrastructure Interference
Minister Bohlin drew a direct parallel between the failed Swedish attack and more successful disruptions seen in Poland. In December, coordinated cyberattacks targeted combined heat and power plants that supplied warmth to nearly 500,000 customers, while simultaneously hitting wind and solar farms. Polish authorities subsequently concluded that the hackers involved were “directly linked to the Russian services.”
The strategy appears to be one of “stress-testing” European resilience. By targeting heating plants during winter months or water utilities during peak demand, these actors aim to create tangible domestic hardship. The goal, according to security officials, is threefold: to erode public support for Ukraine, sow discord within European societies, and force intelligence agencies to drain limited resources on defensive investigations.

The scope of these operations extends beyond the digital realm. In recent months, several European nations have reported physical manifestations of this hybrid strategy:
- Denmark: Officials reported that Russian cyberattacks in 2024 on a water utility resulted in some households losing access to water.
- Norway: In August, police identified pro-Russian hackers who remotely opened a valve in a dam, causing an uncontrolled release of water.
- Latvia: The State Security Service reported in March that railway infrastructure and a train were set on fire by individuals acting in the interests of Russia.
The Anatomy of Hybrid Threats
The transition from traditional espionage to “hybrid threats”—which blend cyberattacks, disinformation, and physical sabotage—represents a shift in how the Kremlin interacts with NATO and EU members. By using “pro-Russian groups” as proxies, Moscow maintains a layer of plausible deniability, even when the technical signatures of the attacks point toward state intelligence services.
| Country | Target | Method | Impact |
|---|---|---|---|
| Sweden | Heating Plant | Cyberattack | Failed attempt |
| Poland | Energy Grid | Cyberattack | 500,000 customers affected |
| Norway | Dam Valve | Remote Hack | Water discharge |
| Denmark | Water Utility | Cyberattack | Localized water loss |
| Latvia | Railways | Arson | Infrastructure damage |
Strategic Implications for Northern Europe
For Sweden, the timing of this admission is significant. As a fresh member of NATO, Sweden is integrating its defense protocols with allies who are increasingly viewing cyber-defense as indistinguishable from territorial defense. The targeting of a heating plant in western Sweden highlights that no region is considered “safe” or too remote to be a target of electronic warfare.
The Kremlin has consistently denied any involvement in sabotage campaigns across Europe, dismissing these accusations as Western fabrications. Still, the consistency of the patterns reported by the North Atlantic Treaty Organization and various national intelligence agencies suggests a centralized strategy of intimidation.
Security experts note that the failure of the attack in Sweden is a testament to improved detection capabilities, but the fact that the attempt occurred at all underscores a persistent threat. The “careless” nature of the attacks mentioned by Bohlin may be intentional—a signal to European capitals that Russia can and will penetrate critical systems if it chooses.
What Happens Next
The Swedish government is expected to continue coordinating with EU and NATO partners to share threat intelligence and harden the defenses of its energy sector. As winter approaches, the vulnerability of heating and power grids remains a primary concern for civil defense authorities across the Baltic and Nordic regions.
Further details regarding the specific group involved in the Swedish attack remain classified, though officials are expected to provide updated guidance on infrastructure security as part of their ongoing civil defense reviews.
We invite our readers to share their perspectives on European security and infrastructure resilience in the comments below.