Windows BitLocker 0-Day Vulnerability: How a Simple USB Can Bypass Disk Encryption
A newly identified Windows BitLocker 0-day vulnerability has demonstrated that the robust disk encryption protecting millions of devices can be bypassed in as little as five minutes. The exploit, which researchers have dubbed the “BitUnlocker” downgrade attack, allows an attacker with physical access to a machine to gain entry to encrypted drives using nothing more than a standard USB stick.
For years, BitLocker has served as a cornerstone of Windows security, designed to protect data-at-rest by encrypting entire drives. By leveraging the Trusted Platform Module (TPM) on a device, BitLocker ensures that even if a hard drive is stolen and placed in another machine, the data remains unreadable. However, this new vulnerability suggests that the very mechanisms intended to facilitate seamless user access can be manipulated to lower the system’s defensive posture.
The discovery comes at a sensitive time for Microsoft, as security researchers continue to uncover a series of zero-day flaws. This particular vulnerability highlights a critical shift in the threat model for enterprise and personal computing: the assumption that physical security is a secondary concern to remote software patches is increasingly being challenged.
The Mechanics of the BitUnlocker Downgrade Attack
The BitUnlocker attack does not attempt to “crack” the underlying AES encryption that BitLocker employs. Instead, it utilizes a “downgrade attack” strategy. In cybersecurity, a downgrade attack occurs when an attacker forces a system to abandon a high-security protocol in favor of an older, weaker, or more permissive one that the attacker knows how to exploit.
In the context of Windows 11 and Windows 10, the vulnerability appears to exploit the way the system handles the transition between different authentication states during the boot process. By using a specially prepared USB device, an attacker can intercept the boot sequence and trick the operating system into reverting to a less secure configuration. This configuration might bypass the requirement for a complex PIN or a hardware-backed key, effectively opening the door to the encrypted volume without the user’s credentials.
Because the attack targets the logic of the boot process rather than the mathematical strength of the encryption itself, the speed of the exploit is remarkably high. Once the USB device is inserted and the boot sequence is manipulated, the time required to access the file system is minimal, making it a highly efficient tool for rapid data exfiltration during physical theft or unauthorized access scenarios.
Why Physical Access Changes the Risk Profile
While many modern security threats focus on remote exploits—malware delivered via email or vulnerabilities in web browsers—this BitLocker flaw falls into the category of physical access attacks. This distinction is vital for how organizations approach risk management. For a remote hacker, BitLocker is an effective barrier; for someone who can physically touch a laptop, the barrier is significantly thinner.
This vulnerability is particularly concerning for industries that handle highly sensitive data, such as legal, financial, or government sectors, where employees often work in public spaces like cafes, airports, or hotels. In these environments, the risk of a device being momentarily unattended is a realistic threat vector. A sophisticated actor could potentially deploy the BitUnlocker attack in a matter of minutes before the owner even realizes the device has been compromised.
The ease of use—requiring only a USB stick—means that the barrier to entry for performing this attack is relatively low. It does not require a massive computing cluster or years of cryptographic expertise; it requires a specific understanding of the Windows boot architecture and the right hardware tool.
The Controversy: Is This a Designed Backdoor?
The discovery of the BitUnlocker vulnerability has sparked a heated debate within the cybersecurity community. Some researchers have pointed out that the ease with which the encryption can be downgraded feels less like an accidental oversight and more like a structural vulnerability that could be interpreted as a “backdoor.”
The argument suggests that if a system is designed to allow for easy recovery or “downgraded” states to prevent users from being locked out of their own data, those same states can be weaponized by attackers. Whether this was an intentional design choice to facilitate law enforcement access or a byproduct of prioritizing user convenience over absolute security remains a subject of significant scrutiny.
While there is no official confirmation that this vulnerability was intended as a backdoor, the technical reality is that the “fail-safe” mechanisms of modern operating systems often provide the very pathways attackers need to bypass primary defenses. This tension between usability and security is a recurring theme in software engineering and BitLocker is currently at the center of it.
Protecting Your Data and Mitigating Risks
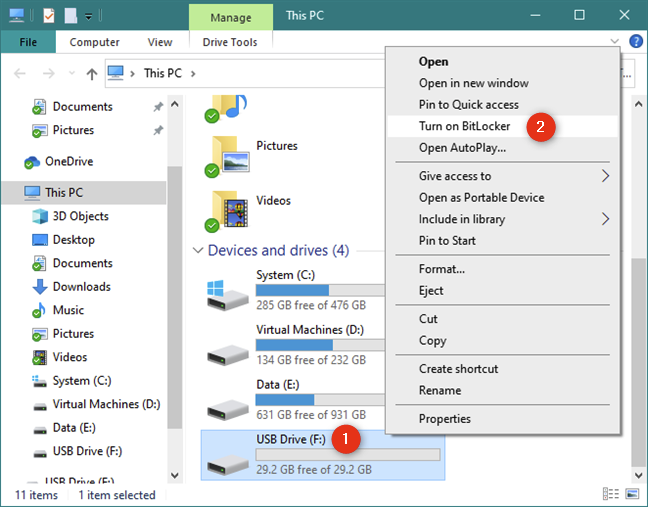
As users and administrators await comprehensive patches from Microsoft, We find several steps that can be taken to harden Windows devices against this type of physical attack. The most effective defense is to move away from “TPM-only” authentication and toward a more robust multi-factor approach.
Implementing a BitLocker PIN or a startup password adds an additional layer of authentication that occurs before the operating system even begins to load. By requiring a manual input that is not stored in the TPM, the window for a downgrade attack to succeed is significantly narrowed, as the attacker would need to bypass both the hardware module and the user-defined secret.
The following table summarizes the differences in security levels between standard configurations and hardened setups:
| Security Configuration | Primary Defense | Vulnerability to BitUnlocker |
|---|---|---|
| TPM-Only Authentication | Hardware-backed keys | High (Susceptible to downgrade) |
| TPM + PIN/Password | Hardware + User Secret | Low (Requires additional credential) |
| Full Disk Encryption (FDE) + External Key | Hardware + Physical Token | Minimal (Requires physical token) |
For enterprise environments, the most critical step is ensuring that all Windows devices are running the latest security updates. Microsoft frequently releases cumulative updates that address vulnerabilities in the Windows bootloader and kernel components. Monitoring for unauthorized USB device usage through Endpoint Detection and Response (EDR) tools can also provide an early warning sign of a physical tampering attempt.
To stay informed on the latest security patches and official guidance, users should regularly consult the Microsoft Security Response Center.
The security landscape continues to evolve as new vulnerabilities are uncovered, and the BitUnlocker discovery serves as a reminder that encryption is only one part of a comprehensive security strategy. The next confirmed checkpoint will be the release of the next scheduled Windows security update cycle, which is expected to include remediations for recent zero-day findings.
We invite you to share your thoughts on this development. How is your organization addressing the risks of physical access to encrypted devices? Let us know in the comments below.

