A security researcher has demonstrated a way to intercept sensitive user data from Windows 11’s controversial Recall feature, using a tool called TotalRecall Reloaded to find a side entrance to Windows 11’s Recall database. Whereas the core database remains encrypted, the tool exploits a weakness in how the system handles data after a user has already logged in.
The discovery highlights a critical gap between the “vault” where data is stored and the “delivery truck” that moves that data to the user’s screen. By targeting a specific system process, the tool can capture screenshots, OCR-processed text, and metadata, effectively riding along with the legitimate user’s session to bypass security prompts.
The researcher, Alex Hagenah, developed the tool to show that while the primary encryption may be robust, the operational pipeline is vulnerable. This method does not require administrator privileges to execute, making it a potentially accessible vector for malicious software to exfiltrate a user’s digital history.
The ‘Delivery Truck’ Vulnerability
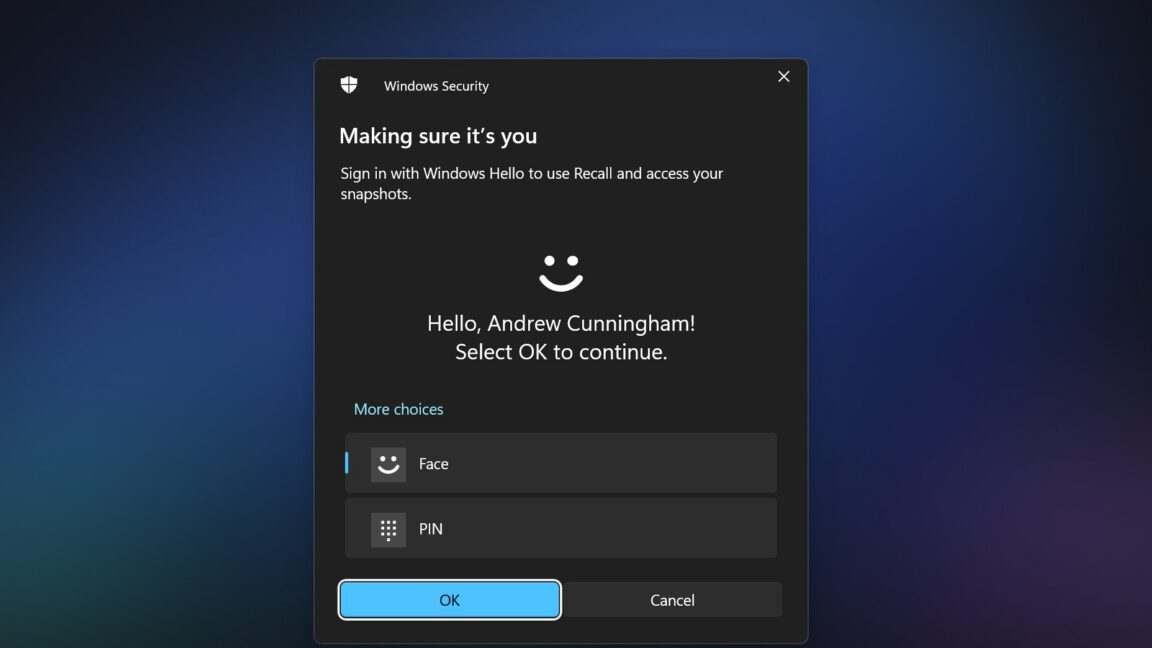
According to documentation on the TotalRecall GitHub page, the primary security of the Recall database is “rock solid.” The system utilizes a Virtualization-based Security (VBS) enclave that refuses to decrypt data without a successful Windows Hello authentication—such as a fingerprint, facial recognition, or a PIN.
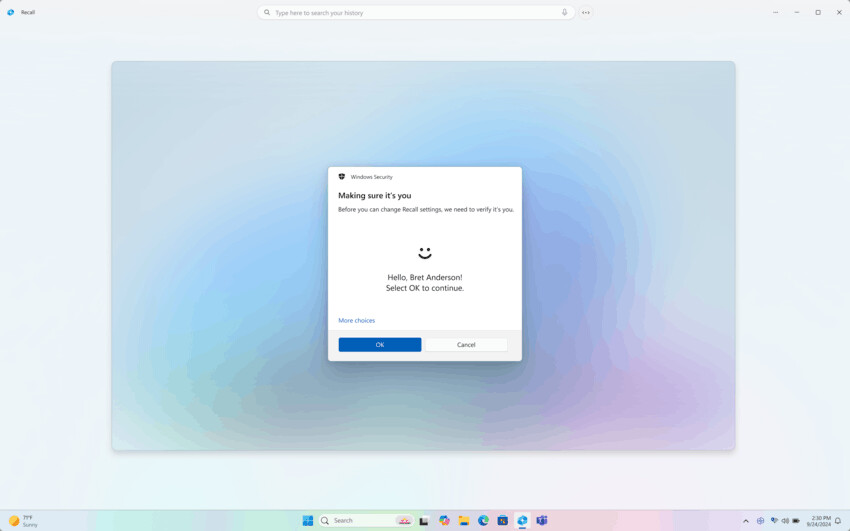
The vulnerability exists in the hand-off. Once a user authenticates via Windows Hello, the system passes the decrypted Recall data to a separate process called AIXHost.exe. Unlike the secure enclave, AIXHost.exe does not possess the same rigorous security protections. This creates a window of opportunity for attackers.
“The vault is solid,” Hagenah writes. “The delivery truck is not.”
The TotalRecall Reloaded tool operates by injecting a Dynamic Link Library (DLL) file into the AIXHost.exe process. Because this injection can be performed without administrator rights, the tool can sit silently in the background. It does not attempt to “crack” the encryption. instead, it waits for the user to perform the authentication themselves. Once the user opens Recall and authenticates, the tool intercepts the data as it is delivered to the process.
Critically, this interception can continue even after the user has closed their Recall session, allowing the tool to maintain a stream of intercepted metadata and screenshots.
What Can Be Accessed Without Authentication
While the bulk of the historical database requires Windows Hello, Hagenah found that certain actions can be performed without any authentication at all. This represents a secondary leak in the system’s perimeter.
- Recent Activity: The tool can grab the most recent Recall screenshot without a prompt.
- Database Metadata: Select metadata regarding the Recall database can be captured.
- Data Destruction: The tool can delete the user’s entire Recall database without requiring authentication.
Once the user provides the necessary Windows Hello credentials, the scope of access expands significantly. The tool can then access both newly recorded information and historical data previously stored in the database.
Microsoft’s Stance and the Timeline
The interaction between the researcher and Microsoft suggests a fundamental disagreement over what constitutes a “vulnerability.” Hagenah reported these findings to the Microsoft Security Response Center (MSRC) on March 6. After reviewing the report, Microsoft officially classified the issue as “not a vulnerability” on April 3.
Microsoft maintains that the discovery is not a bug and has indicated that it does not plan to implement a fix. From the company’s perspective, if a process is already running in the user’s session after authentication, the behavior of AIXHost.exe may be viewed as intended functionality rather than a security flaw.
| Date | Event |
|---|---|
| March 6 | Hagenah reports findings to Microsoft Security Response Center |
| April 3 | Microsoft officially classifies the issue as “not a vulnerability” |
| Post-April | TotalRecall Reloaded tool made available for research on GitHub |
The Broader Implications for AI Integration
As a former software engineer, I’ve seen this pattern before: the “secure core” is often prioritized over the “peripheral plumbing.” In this case, Microsoft built a highly secure vault for the data, but the pipeline used to display that data to the user became the weak link. For users, So that the perceived safety of biometric authentication (Windows Hello) is only as strong as the processes that handle the data after the lock is opened.
This incident underscores the inherent risk of “snapshotting” tools. When a system is designed to record everything a user sees, the database becomes a high-value target. Even if the database itself is encrypted, any process that can read that data—like AIXHost.exe—becomes a proxy for the attacker.
For those concerned about privacy, the ability for a non-administrator tool to delete the entire Recall database without authentication is a double-edged sword. While it allows for quick cleanup, it also means a malicious script could wipe a user’s history without their knowledge or consent.
The next step for the community will be to see if other researchers can find similar “side entrances” in other AI-integrated Windows processes. As Microsoft continues to roll out Copilot+ features, the scrutiny on how these processes interact with the VBS enclave will likely intensify.
Do you use Windows Recall, or have you disabled it for privacy reasons? Share your thoughts in the comments below.