For many compact business owners in Switzerland, the digital tools meant to streamline their accounting have recently become a source of profound anxiety. A sophisticated phishing campaign targeting users of Bexio, the country’s leading management software, has left several companies grappling with compromised data and diverted funds.
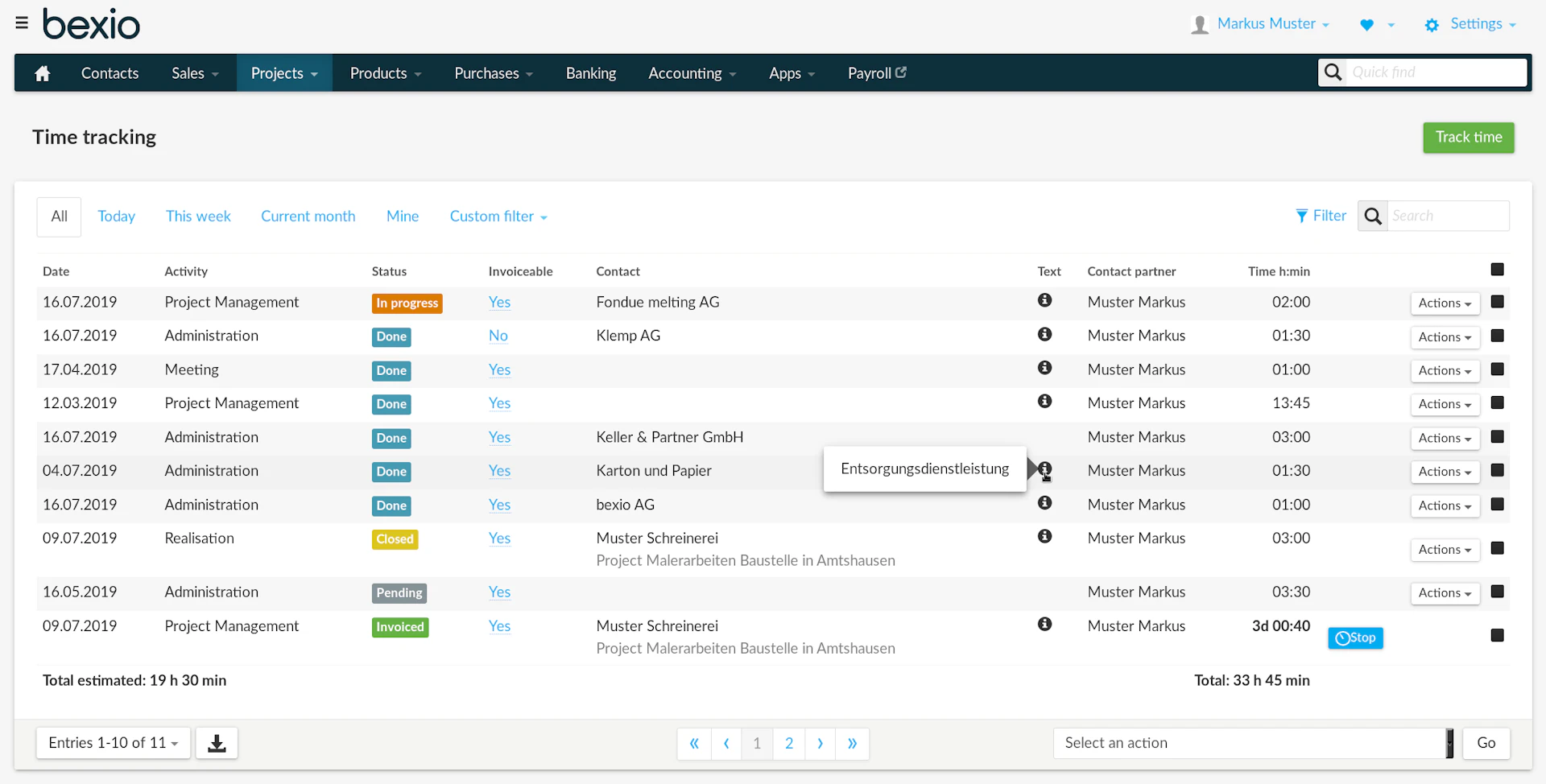
The attack did not involve a breach of Bexio’s central servers, but rather a calculated exploitation of human trust. By tricking users into surrendering their credentials through fraudulent emails, cybercriminals gained access to individual accounts. Once inside, the attackers didn’t just steal data—they weaponized it, altering bank details on outgoing invoices to redirect payments from unsuspecting clients into fraudulent accounts.
Bexio, a subsidiary of the insurance giant La Mobilière, serves more than 100,000 clients across Switzerland, the vast majority of whom are small and medium-sized enterprises (SMEs). Because these businesses rely on the software for everything from payroll to client registries, the breach of a single account can compromise the entire financial chain of a company and its partners.
The Anatomy of a ‘Business Email Compromise’
The tactics employed in the Bexio campaign are classic examples of Business Email Compromise (BEC), a growing menace that the Swiss National Cyber Security Centre (NCSC)—known in French as the Office fédéral de la cybersécurité (OFCS)—has repeatedly warned against. Unlike a traditional “hack” where a firewall is bypassed, BEC relies on social engineering.
In this instance, the attackers used external servers to send phishing emails that mimicked official Bexio communications. When a user clicked a link and entered their login details on a spoofed page, the criminals gained a “key” to the business’s financial heart. Once they accessed the account, they performed a surgical manipulation: changing the IBAN (International Bank Account Number) on invoices.
One affected client reported that the hackers modified bank coordinates and stole personal data, allowing the fraudsters to send authentic-looking invoices to the company’s own customers. The result is a domino effect of fraud where the victimized SME loses revenue, and their clients unknowingly fund a criminal enterprise.
| Stage of Attack | Action Taken by Criminals | Impact on Business |
|---|---|---|
| Intrusion | Phishing emails capture user credentials | Unauthorized account access |
| Manipulation | IBANs and payment details are altered | Financial records are corrupted |
| Diversion | Fraudulent invoices sent to clients | Payments routed to attacker’s account |
| Exfiltration | Personal and client data harvested | Potential GDPR/Data privacy violations |
Bexio’s Response and the 2FA Mandate
Thommy Rüegg, Bexio’s Director of Communications, has been clear that the company’s internal IT systems remained secure throughout the offensive. “The sending of fraudulent emails is carried out via third-party networks,” Rüegg stated, noting that because the attack originated externally, it is difficult to quantify exactly how many messages were sent.
In response to the campaign, Bexio has shifted from recommending security measures to enforcing them. The company has now made two-factor authentication (2FA) mandatory for all clients. This critical security layer requires a second form of verification—such as a code sent to a mobile device—meaning that even if a user accidentally gives away their password on a phishing site, the attacker still cannot access the account.
The company’s technical support team, based in the canton of St. Gallen, is currently prioritizing reports of suspicious activity. Bexio has also launched a dedicated information page to guide users through security protocols and recovery steps.
A Systemic Vulnerability for Swiss SMEs
The Bexio incident is not an isolated event but part of a broader trend of cyber-aggression targeting the Swiss economy. Small businesses are often the “soft underbelly” of the corporate world; they possess valuable data and handle significant financial transactions but often lack the dedicated cybersecurity departments found in larger corporations.
The NCSC has highlighted that the increase in BEC attacks is often linked to the digitalization of the Swiss workforce, where the lines between official communication and digital noise have blurred. When an invoice looks correct and comes from a trusted software platform, few business owners think to call their provider to verify a change in bank details.
Beyond the immediate financial loss, the administrative burden of such an attack is immense. Companies must conduct deep forensic audits to ensure no other data was altered and, in severe cases, must notify the Federal Data Protection and Information Commissioner (FDPIC) if personal data has been leaked.
Disclaimer: This article is provided for informational purposes only and does not constitute legal or financial advice. Businesses suspected of being victims of cybercrime should consult with certified cybersecurity professionals and legal counsel.
Victims of this or similar attacks are urged to report the incident immediately to the National Cyber Security Centre via their official reporting form and to file a formal complaint with their respective cantonal police department.
As the investigation into the identity of the attackers continues, the focus now shifts to the wider adoption of “Zero Trust” architectures among Swiss SMEs. The next critical checkpoint will be the NCSC’s upcoming quarterly threat report, which is expected to detail whether the Bexio campaign was a standalone operation or part of a coordinated effort by a larger state-sponsored or criminal syndicate.
Do you have experience with phishing attempts or tips for securing your business accounts? Share your thoughts in the comments below or share this article with other business owners to help them stay vigilant.
